To Pay or Not To Pay: Resolving Frauds in Auction with Mobile Payment
全文
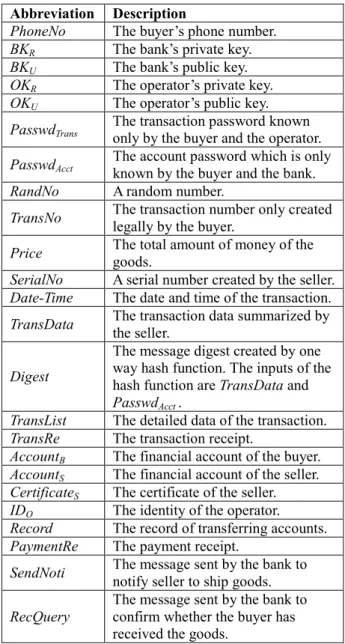
(2) auction website or Escrow Service provider. The buyer can transfer the payment to the mediator after making purchases on the auction website. The mediator notifies the seller to ship the items when the mediator receives the payment. The buyer notifies the mediator when the merchandise is receiving and is satisfactory. The mediator will then release the payment to the seller. eBay in America and one auction website in China are using this method and eBay cooperates with Escrow Service provider[1]. This method is useful for large sales, but is not convenient for low value transactions. In addition, it will take a longer time to finish a transaction [2]. The second method is like Sotheby's auction. There is also a mediator, who is assumed to be trustworthy. The mediator is commissioned by the seller to auction the items. First, the seller ships the items to the mediator. If a buyer wants to make purchases, he/she has to transfer the payment to the mediator. The mediator will ship the items to the buyer and transfer the payment to the seller then. The mediator would charge commissions. Those two resolutions seem to solve the online auction frauds, but users might still suffer loss if they link to a fake website taking the wrong information about making payment such as the account to accept payment. Phishing and Pharming are techniques which make the users enter forged webpages. Phishing is a kind of frauds, which combines the internet technology and soft engineering to tempt users to enter the fraudulent website. For examples, sending mails tempting users to click the fake links [3] [4]. Pharming is harder to be identified, because it directly attack DNS server by some network technologies. Even though users key in correct URL, they will still enter the fake website, which provide the false account for making a payment. The methods of frauds could be much more than what mentioned above, so a securer mechanism is necessary to ensure the security of online auction.. bank, only know the total amount in the transaction instead of the actual items. There are two assumptions in the mechanism: The operator and banks are trustworthy and will not disclose the sensitive information of the users. The buyer has surely become the winning bidder of certain items. The detail of our payment mechanism is illustrated in next paragraph, and the abbreviations of the relevant data used in the payment system are shown in Table 1. Table 1. Abbreviations of the data used in the proposed mobile payment system Abbreviation PhoneNo BKR BKU OKR OKU PasswdTrans PasswdAcct RandNo TransNo Price SerialNo Date-Time TransData Digest TransList TransRe AccountB AccountS CertificateS IDO Record PaymentRe. 3: Solution with Mobile Payment We propose a mobile payment mechanism to solve the frauds more effectively. There are two trustworthy mediators beside sellers and buyers in our mechanism. The operator and the banks are the mediators, who take charge of the verification of seller and buyer and the transaction. The operator verifies the buyer through the cell phone number and the password of transaction. The bank also verifies the buyer through his/her financial account. Additionally, the bank manages the account of the buyer, so the greatest benefit of our model is that the buyer could transfer the payment by his/her bank after receiving the goods. This benefit makes our mechanism different form current payment ways of online auctions. Security of our payment mechanism is enhanced by asymmetric encryption and one-way hash function. The participators are hard to be faked. Beside security, our model also provides transaction privacy to buyers. The mediator, the operator and the. SendNoti RecQuery. Description Th ebu y e r ’ sph on enumbe r . Th eba n k’ spr i v a t ek e y . The bank’ spu bl i ck e y . Th eope r a t or ’ spr i v a t ek e y . Th eope r a t or ’ spu bl i ckey. The transaction password known only by the buyer and the operator. The account password which is only known by the buyer and the bank. A random number. The transaction number only created legally by the buyer. The total amount of money of the goods. A serial number created by the seller. The date and time of the transaction. The transaction data summarized by the seller. The message digest created by one way hash function. The inputs of the hash function are TransData and PasswdAcct . The detailed data of the transaction. The transaction receipt. The financial account of the buyer. The financial account of the seller. The certificate of the seller. The identity of the operator. The record of transferring accounts. The payment receipt. The message sent by the bank to notify seller to ship goods. The message sent by the bank to confirm whether the buyer has received the goods.. 3.1: Overview of the Payment Process The participators in our payment mechanism include: buyers, sellers, the operator, and banks. 1) Buyer: To make a transaction with the seller, the buyer needs to apply to the operator for the mobile payment service. 2) Seller: The seller provides auction goods to buyers.. - 791 -.
(3) 3) Operator: The operator has to confirm the transaction with the buyer. The operator has to check whether the buyer is a legal subscriber of the mobile payment service. 4) Bank: The bank is responsible for the verification of buyers and sellers and settlement of accounts.. Seller: Seller can communicate with the operator or the bank through the Internet. For the security concern, the seller need to apply for a digital certificate to prove his identity to the bank and download the certificate of the operator and the bank issued from the trusted certificate authority (CA). The certificate of the operator/bank includes the public key of the operator/bank, which is needed in our mechanism. Operator: As for the operator, they have to maintain additional data in the database, such as the transaction passwords, the corresponding phone number and the identities of the bank of the buyers who has applied for the mobile payment service. The operator also applies for its digital certificate and downloads all cooperative ba n k s ’c e r t i f i c a t e sf r om CA.Th eope r a t orh a s asymmetric keys for data encryption, includes the public keys of all cooperative bank. Bank: The bank also has to store additional data in the database, such as the account password (PasswdAcct) of the consumer which is different from the password of the cash card. Besides, the bank needs to maintain the transaction record for future inquiries. The same with the operator, the bank need to apply for its certificate, too.. There are three phases in our payment scheme: initiation phase, transaction phase, and settlement phase. initiation phase This phase includes the required preparations of each participant before the payment mechanism performs. transaction phase and settlement phase As an illustration, the steps in transaction phase and settlement phase is shown in Fig. 2. Seller. Buyer. Operator. Bank. 1. •TransNo •IDO. transaction phase. 2(a). TransList 2(b). [TransData]OKU 3. TransData 4.. Digest [TransData || Digest. 5. || Account ] BK B U 6(a). [SendNoti] BKR 6(b). RecQuery settlement phase. 7. [ RecQuery || PasswdAcct ] BKU 8(a). Record 8(b). PaymentRe 9. TransRe. Fig.2. Data flow of transaction procedure. 3.2: Interactions between the Participators We now describe the interactions between the participants for each phase. 1) Initiation phase. Buyer: First, the buyer should have the mobile device, such as cell phone or PDA which the telecommunication module is embedded in. The mobile device must have the capability of data storage and cryptographic computing. The buyer applies for the mobile payment service and transfers his financial account (AccountB) to the operator. Then, the operator issues a personal transaction password and the public key of the operator (OKU) to the buyer and stores the key in the SIM card of the cell phone. To reduce the waiting time of transaction, the buyer could generate the transaction number in advance before the transaction. The transaction number is created by using theope r a t o r ’ spu bl i c key to encrypt the consumer’ s phone number, transaction password, and a random number.. 2) Transaction phase. In step 1), the buyer transfers the transaction number (TransNo) and the identity of the operator (IDO) to the seller. The transaction number is a ciphertext encrypted by using the public key of the operator. As mentioned in initiation phase, the transaction number is g e n e r a t e dbyus i n gt h eope r a t or ’ spu bl i ck e yt oe n c r y pt t h ec on s ume r ’ sph on en umbe r( Ph on e No) ,t r a n s a c t i on password (PasswdTrans), and a random number (RandNo). The random number is generated by the cell phone and used to make the transaction number dynamic. The operator could verify the buyer by the data in the transaction number. The transaction number could only be decrypted byt heope r a t o r ’ spr i v a t ek e y . In step 2a), the seller summarizes the required information into the transaction data list (TransList), and sends it to the buyer as a verification of this transaction. All details about this transaction such as the transaction number, the transaction date, the serial number, the item name, unit price and total amount of money are included in this transaction data list. The buyer could view the list on the browser. In step 2b), the seller summarizes the required information into the transaction data (TransData), and encrypt st h et r a ns a c t i onda t abyu s i ngt h eope r a t or ’ s public key. The seller transmits the transaction data to the operator according to the IDO of the buyer for the further confirmation. The transaction data includes the transaction number, the transaction date, the serial n umbe r ,s e l l e r ’ sf i n a n c i a la c c ou n t ,s e l l e r ’ s di g i t a l certificate and total amount of money. The transaction data would not contain the details of the goods to ensure the transaction privacy of the consumer. Only the seller. - 792 -.
(4) Seller Input. Buyer. Process. • TransNo •Date-Time •SerialNo •AccountS •Price •Certificate S. Output Buyer TransRe •TransList. Input. Process. Output. •TransData. One-way hash function. Digest. •Passwd Acct. Summarize. Operator. •TransData. Fig.5. Step 4 in transaction phase. Input. Process. Output. TransData. Encrypt by OKU. [TransData]OKU. Operator. Fig.3.Step 2 in transaction phase knows the goods the buyer bids. The transaction data in step 2a and step 2b are shown in Fig. 3. Operator Input. Process. Output. [TransData]OKU. Decrypt by OKR. TransData. Seller. Input. Process. Output. TransNo. Decrypt by OKR. •PhoneNo •RandNo •PasswdTrans. transmits the message digest back to the operator to finish the transaction confirmation as depicted in Fig. 5. The operator will transmit the message digest to the bank for further verify. Using one-way hash function to produce the message instead of encryption with the public key of the bank is because of the speed of one-way hash function is faster than that of the encryption. But if the buyer rejects the payment or enters the wrong PasswdAcct three times, the operator will transfer a message to inform the seller about the breach of the transaction. In step 5), the operator has to forward relative data to the bank for further check. The operator will receive the message digest from the buyer if the transaction exists and the transaction data is confirmed by the buyer. The operator encrypts the transaction data, the message di g e s t ,a n dt h ebuy e r ’ sba nka c c ou n t( Ac c ou nt B) with t h eba nk’ spu bl i ck e y( BKU) and transfers these data to the cooperative bank for verifying the buyer and recording the transaction.. Buyer Input. Process. Output. PasswdTrans. Verify. TransData. Bank Input. Process. [ TransData || Digest || AccountBC ] BKU. Fig.4. Step 3 in transaction phase In step 3), the operator takes charge of the verification of the buyer and the transaction. After the operator receives the transaction data (TransData) from the seller, it decrypts the transaction data with its private key (OKR) to get the transaction number. The operator further decrypts the transaction number and verifies the buy e r ’ st r a ns a c t i on pa s s wor d( PassdTrans). If no error occurs in the verification, the operator will transfer the transaction data to the buyer through USSD connection f orf u r t h e rc h e c ka n dwa i t sf ort h ec on s ume r ’ s response as depicted in Fig. 4. Making the buyer check the transaction data prevents the seller from interpolating the transaction content and fabricating the transaction transferred to the operator. In step 4), the buyer has to confirm the transaction data delivered by the operator. If the transaction information is correct, the consumer has to input the account password (PasswdAcct) as a confirmation of his identification. The cell phone will hash the transaction data and the account password by a hash function. After the hash function being performed, it will create a message digest (Digest). Finally, the consumer. Input •TransData •PasswdAcct Input •SendNoti. Input SerialNo • •Account B. Decrypt by BKR. Process •One-way hash function •Compare with Digest Process •Encrypt by BKR Process •Summarize. Output. Operator. •Digest •Account B •TransData Output •SendNoti. Output. Seller. goods. •[SendNoti] BKR Output •RecQuery. Buyer. Fig.6. Step 6 in transaction phase In step 6a), as shown in Fig. 6, when the bank receives the encrypted data from the operator, it uses its private key (BKR) to decrypt the ciphertext getting the buy e r ’ s di g e s t ,t h e buy e r ’ sf i n a n c i a la c c ou nt a n d transaction data. The bank authenticates the seller by verifying its certificate contained in the transaction data. The bank can find the account password of the buyer by. - 793 -.
(5) the corresponding financial account. Then the bank calculates the hash function over the concatenation of the transaction data and the account password of the buyer. If the comparison between the output of the hash function and the message digest from the operator is the same, which means the buyer doesn’ t interpolate the TransData,t h e ba n k wi l lf u r t h e rc h e c kt h e buy e r ’ s credit line and transmit a message, which is encrypted by its private key (BKR) ([SendNoti]BKR), notifying the seller to deliver the goods to the buyer. The SendNoti is truly sent by the bank if the seller can decrypt that cipher text by using the bank’ s public key (BKU). The seller can send the goods according to the serial number involved in that notification. In step 6b), the bank sends a query (RecQuery) to ask whether the buyer receive the goods. The query contains the serial number for the buyer to identify the transaction. The bank will complete account settlement after receiving the reply from the buyer. The process in step 6b is shown in Fig. 6. 3) Settlement phase. Buyer Input. Process. •RecQuery Encrypt •Passwd Acct by BKU. Output [ RecQuery TransData Account C ] BK BK U || ||Passed Acct. Bank. Fig.7. Step 7 in settlement phase In step 7), after the buyer receives the query, he/she identifies the transaction according to the serial number. When receiving the goods, the buyer input the account password (PasswdAcct). The cell phone encrypts the account password and the query with the bank’ s public key to create a cipher text as a reply and send it to the bank as shown in Fig. 7. The bank will start the account settlement when noticing that the buyer has received the goods. Bank Input. Process. Output. Buyer. Decrypt •RecQuery [ RecQuery TransData AccountAcct || ||Passed C ] ]BK BK U by BK R •PasswdAcct Operator Process. Input •TransData PasswdAcct. •Verify. Output •Record •PaymentRe. Seller. Fig.8. Step 8 in settlement phase The bank will receive a reply from the buyer if the buyer actually receives the goods. The bank can get the. buy ’ spa s s wor doft h ea c c ou n ta n dt h equ e r ywhi c h includes the serial number by decrypt the reply. The bank can find the account password of the buyer by the corresponding financial account recorded in the transaction records. If the password is correct, the bank will complete the account settlement. Then the bank transmits the transaction record to the operator for avoiding the possible dispute (step 8a) and also transfers the payment receipt (PaymentRe) to the seller (step 8b) as shown in Fig. 8. The seller could show the transaction receipt (TransRe) on the browser for the consumer to check and print. Every transaction has to go through the transaction phase and settlement phase.. 4: Discussion 1) Our mechanism can avoid fraud, because the bank will perform the account settlement after the goods really received by the buyer who is verified by the operator and the bank. If the seller does not ship the items in purpose, the buyer will not reply the bank for completing the account settlement. In respect of another situation, if someone pretends to be the seller sending mail includes fake remitting information, the buyer will not be fooled, for buyer need not make the payment before get the goods and the seller actually would not contact with the buyer by mail in our mechanism. 2) Our mechanism can prevent buyers duping from phishing and pharming, for buyers do not need to make the payment before getting the goods. Even the buyer enters fake website bidding something and the cheater imitate the process to transact with the buyer, the fraud will still fails since the buyer will not notify the bank to make the account settlement without receiving the items. 3) Ou rme c h a n i s mpr ot e c t sbuy e r s ’t r a n s a c t i onpr i v a c y . The operator and the bank cannot acquire the detail of the merchandise purchased by the buyer except the total amount of the merchandise. Although only the seller knows what the buyer purchases, the seller c a n ’ ts hi pt h eg oodwh i c hi s n ’ tme e t i ngt h ei t e m description outlined on the website, or the seller won ’ tr e c e i v et h epa y me n t .Besides, the transferred data with encryption of the asymmetric cryptography is hard to be broken [5]. 4) Beside privacy, our mechanism also meets security criteria which includes confidentiality, authentication, integrity, and non-repudiation. Confidentiality. As for data storage, the sensitive data of transaction and the encryption keys are stored in the SIM card which is a tamper-resist device. The verification of the PIN and the PasswdAcct prevent the cell phone from misusing by someone else. As for data transmission, the data between the seller and the operator or between the operator and the bank can be transferred through the wired network such as ADSL, which use SSL. - 794 -.
(6) transaction protocol to ensure the security of data. In our payment scheme, the data transferred in the wired network is protected by the public-key based algorithm which can prevent the confidential attack effectively [6]. Besides, the secure connection of USSD between the operator and buyer is provided by the signal protection mechanisms of GSM/UMTS [7]. Authentication. The buyer is authenticated three times in our payment mechanism: a) The cell phone verifies the PIN of the buyer. b) The operator verifies the PasswdTrans. c) The bank verifies the PasswdAcct of the buyer. With those tree authentications, the risk of counterfeit is reduced to the minimum. As for the seller, the bank authenticates the seller by verifying its certificate. The certificate of the seller is issued from the trusted third party which could be the governmental institution. Integrity. The seller summarizes the TransList to the buyer and show TransRe to the consumer after the account settlement. The operator forwards TransData to the buyer for checking. The bank transfers a PaymentRe to the buyer after the account settlement. These data can be combined through the SerialNo of the transaction. The buyer can ensure the integrity of the transaction by comparing these data. Non-repudiation. After the buyer confirms the transaction, he has to enter the PasswdAcct for the calculation of message digest. Then, the bank authenticates the buyer by verifying the message digest. Only the legal buyer and the bank can calculate the same Digest because the PasswdAcct is only known by them. The transaction is confirmed if the Digest was correctly verified, and the buyer cannot deny the transaction.. 5: Conclusion Many people purchase goods by online auctions and online auction fraud is gradually prevalent nowadays. We propose a mobile payment mechanism to protect numerous customers from auction fraud. The participators in our payment mechanism include: buyers, sellers, the operator, and banks. The operator and the banks are mediator, verifying seller, buyer and the transaction. The bank also acts like an Escrow Service provider mentioned above. Even if the buyer receives the items without replying the bank, the seller still can ask the bank to transfer the payment by some other process, for the bank manages the account of the buyer. The process is that after the operator and the bank verify the buyer by some data transferred between the four participators, the bank will notify the buyer to ship the items. Then the bank will complete the account settlement after the buyer receives the items and send the reply to the bank.. Our payment mechanism provides many advantages: 1) Security: Our payment scheme meets security criteria, which includes integrity, confidentiality, authentication, and non-repudiation. Besides, the risk can be minimized when the consumer loses the cell phone or the cell phone is forged because our method provides multiple authentications. Besides, auction fraud, Phishing and pharming can be resolved, for our unique designation. Buyers can make the actual payment after receiving the goods. 2) Transaction privacy: The operator and the bank cannot acquire the detail of the merchandise purchased by the consumer except the total amount of price. 3) Convenience: The time of the transaction is shortened because the buyer needs not to send remittance to the mediator compared with the method mentioned in the section 2. Beside the time-saving, the cost of the transaction can be lower. 4) Low computational load of the mobile phone: The operation of the consumer in the transaction phase can be only a one-way hash function. The speed of one-way hash function is about 100 times faster than that of the encryption/decryption of the secret-key system and the speed of the encryption/decryption of the secret-key system is about 100 times faster than that of the signature/verification of the public key system [8]. 5) Feasibility: The participators can adopt our payment scheme into their business model without additional cost of hardware. And it is implemented based on the existing network environment.. References [1] eBay, http://pages.ebay.com/help/tp/payment-escrow.html [ 2 ]Su l i nBa,Andr e w B.Whi ns t on,Ha nZha ng ,“ Bui l d i ng trust in online auction markets through an economic i nc e nt i v eme c ha ni s m” ,De c i s i on Sup por tSy s t e ms ,v . 35 n.3, p.273-286, June 2003. [3] Wenyin Liu, et al, “ Phishing Web page detection” , Document Analysis and Recognition, 2005. Proceedings. Eighth International Conference on, Vol. 2, p.560-564, Sept. 2005. [4] E. Kirda, C. Kruegel, “ Protecting users against phishing attacks with AntiPhish” , Computer Software and Applications Conference, 2005. COMPSAC 2005. 29th Annual International, Vol. 2, p.517-524, July 2005 [5] Da v i d Poi nt c he v a l ,“ As y mme tric cryptography and pr a c t i c a ls e c ur i t y ” ,J our na lofTe l e c ommuni c a t i onsa nd Information Technology, no. 4, p. 41–56, April 2002. [6] William Stallings, Network Security Essentials, Prentice Hall, 2000. [7] S.Sc hwi de r s k iGr os c hea ndH.Kn os pe ,“ Se c ur emobile c omme r c e ” ,El e c t r oni c s& Communication Engineering Journal, p.228- 238, October 2002. [8] Wei-Bin Lee, Chang-KuoYe h ,“ ANe wDe l e g a t i on-Based Authentication Protocol for Use in Portable Communi c a t i onSy s t e ms ” ,I EEETr a ns a c t i onsonWi r e l e s s Communications, Vol. 4, No. 1, p. 57- 64, Jsanuary 2005. - 795 -.
(7)
數據
相關文件
2.1.1 The pre-primary educator must have specialised knowledge about the characteristics of child development before they can be responsive to the needs of children, set
Reading Task 6: Genre Structure and Language Features. • Now let’s look at how language features (e.g. sentence patterns) are connected to the structure
Understanding and inferring information, ideas, feelings and opinions in a range of texts with some degree of complexity, using and integrating a small range of reading
Writing texts to convey information, ideas, personal experiences and opinions on familiar topics with elaboration. Writing texts to convey information, ideas, personal
Promote project learning, mathematical modeling, and problem-based learning to strengthen the ability to integrate and apply knowledge and skills, and make. calculated
Now, nearly all of the current flows through wire S since it has a much lower resistance than the light bulb. The light bulb does not glow because the current flowing through it
During early childhood, developing proficiency in the mother-tongue is of primary importance. Cantonese is most Hong Kong children’s mother-tongue and should also be the medium
Writing texts to convey simple information, ideas, personal experiences and opinions on familiar topics with some elaboration. Writing texts to convey information, ideas,