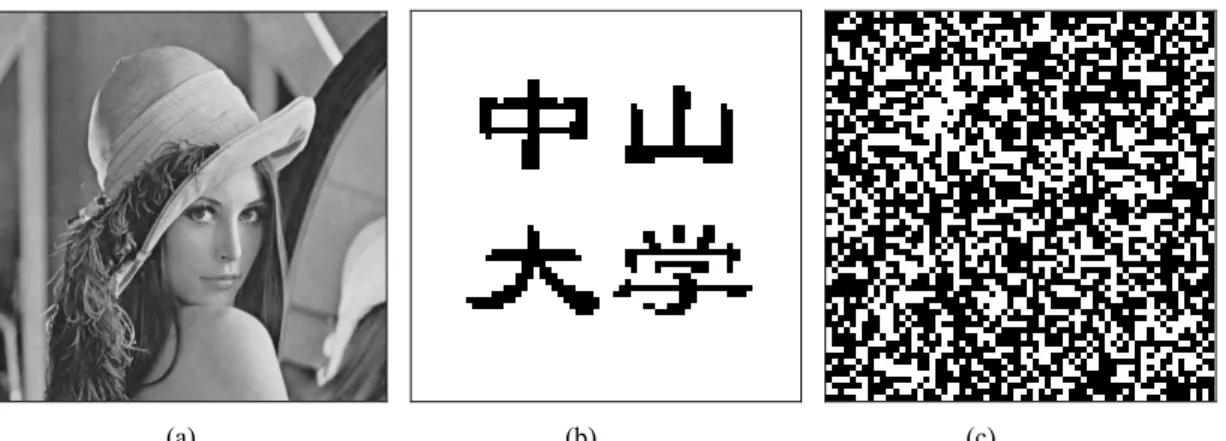
Secure Semi-Fragile Watermarking for Image Authentication Based on Parameterized Integer Wavelet
全文
數據
相關文件
This kind of algorithm has also been a powerful tool for solving many other optimization problems, including symmetric cone complementarity problems [15, 16, 20–22], symmetric
Local, RADIUS, LDAP authentication presents user with a login page. On successful authentication the user is redirected to
(Another example of close harmony is the four-bar unaccompanied vocal introduction to “Paperback Writer”, a somewhat later Beatles song.) Overall, Lennon’s and McCartney’s
It is based on the goals of senior secondary education and on other official documents related to the curriculum and assessment reform since 2000, including
Carve if not photo- -consistent consistent Project to visible input images Project to visible input images. Multi-pass
Carve if not photo- -consistent consistent Project to visible input images Project to visible input images.. Multi-pass
It is interesting to discover that the golden ratio appears not only in the fluid sink and heat source induced maximum ground surface horizontal displacements, but also on
Therefore the existing transportation system has not been considering the characteristics of female users.This is an original study trying to investigate the differences