IEEE COMMUNICATIONS LETTERS, VOL. 8, NO. 7, JULY 2004 431
Radio Resource Index for WCDMA Cellular Systems
Scott Shen, Student Member, IEEE, and Chung-Ju Chang, Senior Member, IEEE
Abstract—In this letter, a radio resource index (RRI) is derived to
estimate the radio resources of a connection in WCDMA cellular systems. An analytical model is presented and large deviation tech-niques are used. The RRI can transform traffic parameters and multiple quality-of-service (QoS) requirements into a measure of radio resources using a unified metric.
Index Terms—Radio resource index (RRI), large deviation,
WCDMA.
I. INTRODUCTION
A
LGORITHMS for allocating radio resources to a connec-tion request have been addressed in the literature [1], [2]. These algorithms just allocate appropriate power to the con-nection to meet the required bit error rate (BER). However, in the quality-of-service (QoS) architecture of wideband CDMA (WCDMA) [3], more QoS requirements, such as packet drop-ping ratio and delay, should be considered for estimating radio resources.This letter derives a radio resource index (RRI) for a connec-tion in WCDMA cellular systems, based on not only BER to meet the packet-level requirement but also the packet dropping ratio and the tolerable delay to meet the call level requirements. The RRI specifies the equivalent amount of power required to fulfill the above three requirements of the connection with spe-cific traffic characteristics. It performs as a function that maps from a parametric space, defined by traffic parameters and QoS requirements, to the metric space, while guaranteeing the QoS requirements for all existing calls. The calculation of RRI is independent of the dimensions of traffic types, parameters and QoS requirements. The RRI is useful for solving radio resource management problems, such as call admission control and radio bearer control.
II. SYSTEMMODEL
Consider connections using shared channels in the uplink. The connection is assumed to be bursty such that packets ar-rive in batches. The head-of-line packet of a burst is firstly sent as a request for a resource reservation, where the permission probability of access is broadcasted by the radio network con-troller. If the first packet is not permitted to transmit in this frame or is transmitted but corrupted on the air interface, it will retry.
Manuscript received November 4, 2003. The associate editor coordinating the review of this letter and approving it for publication was Prof. J. Evans. This work is supported by National Science Council, Taiwan, R.O.C., under Contract NSC 92-2219-E-009-025.
The authors are with the Department of Communication Engineering, National Chiao Tung University, Hsinchu 300, Taiwan, R.O.C. (e-mail: [email protected]).
Digital Object Identifier 10.1109/LCOMM.2004.832756
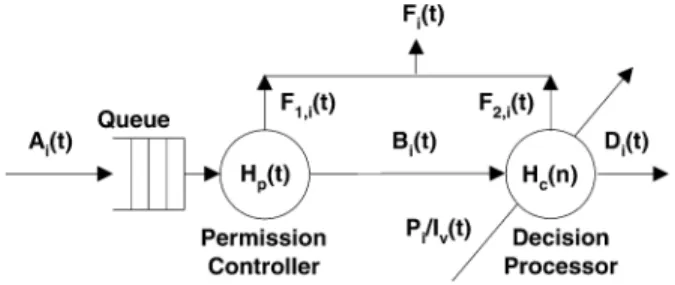
Fig. 1. The analytical model of the uplink connectioni in WCDMA.
If the first packet fails to transmit successfully or is acknowl-edged before the maximum tolerable delay, then all packets in the burst are dropped. Once the first packet has been success-fully acknowledged, the remaining packets of the burst can be sent in sequence without any further request. The receiver will discard any packet sent out but corrupted in the air interface. The signal-to-interference ratio for connection , in terms of the BER requirement and spreading factor setting, is set to deter-mine whether the packet is successfully received or discarded. All the packets dropped due to either excess delay or channel error are attributed to the failure process. The maximum system load is denoted by and the target received power for a basic rate transmission of connection to achieve is denoted by . Equal received power control is adopted. Also, the call-level QoS requirements of connection are assumed to be the packet dropping ratio, , and the maximum tolerable delay, .
Fig. 1 presents the analytical model for uplink connection , where the general capital letter represents the cumulative
process of a process , that is, .
de-notes the arrival process of user . represents the access process for arrivals to the permission controller, where packets are permitted or dropped. The dropped packets are directed to-ward a failure process denoted by ; the permitted packets form an output process, denoted by . Subsequently, the permitted packets in enter into the decision process, rep-resented by . The decision processor determines the di-rection of the packet, in terms of the amount of the aggregated interference process, denoted by , which is the sum of the adjacent-cell interference and the home-cell interference . The received power of the transmission packet of con-nection forms a process on the air interface, and rep-resents the power component contributed by connection to
the transmission channel. If is less than , then
the packet will be directed to a failure process ; other-wise, the packet will be successfully received and forms a de-parture process, denoted by . Notably, for convenience, including interference of user is assumed, which would be the upper bound on the interference received by each user.
432 IEEE COMMUNICATIONS LETTERS, VOL. 8, NO. 7, JULY 2004
III. ANALYSIS
The stochastic process is characterized by using a log-scale generating function, called the cumulant generating
func-tion, defined as , and the
limit is assumed to exist and to be differentiable [4]. By the cumulant generating function, we can easily characterize the
output processes of and in terms of behaviors of
and and their input processes. Consequently, the , denoting the equivalent power generated by connection with its QoS requirements guarantee, can be estimated.
Theorem 1: For a given cumulant generating function
, and to be the solution to , the
received power for the basic rate transmission of connection , required to fulfill and , should be set to
(1) where denotes the successful access probability in the per-mission controller. The RRI of connection , in terms of the cu-mulant generating function of input process and the re-ceived power , is given by
(2) Also, the packet dropping ratio of each connection can be guaranteed if the following constraint is satisfied,
.
The ratio varies from the mean rate to the peak rate of the process as goes from to . By the Taylor expansion of the cumulant generating function, is the best weighting of each existing order of the moments of the process and depends on the setting of the system. Several lemmas are presented before the above results can be derived.
Lemma 1: The failure process has a cumulant gener-ating function
(3) Proof: For an arrival process , we construct its corre-sponding marked point process, by counting the number of arrival bursts , before time . Define as the time at which
the th burst arrives, and if and , otherwise.
Since the th burst shall request for permission and may fail to access the resource, the permission controller can be modeled to a server with vacation of probability . Thus, the access
process is given by , where is 1 if
and the -th burst arrival’s access succeeds;
is 0, otherwise. Then, and is
Notably, can be obtained by
, where is the outage probability of
con-nection , given by (4), and .
The cumulant generating function of can be directly
given by .
Lemma 2: The outage probability of connection , re-lated to the aggregated interference , is
(4) where is the number of connections,
, and is the rate function of the interference process.
Proof: is the rate function measuring the expo-nential decay rate on the event with respect to the aggregated
interference process can be defined by the
Le-gendre Transform [4] of its cumulant generating function . The result of the unbuffered resources model in [5] states that if the aggregation of random variables at time , denoted by , exceeds the capacity , then the large deviation approximation to the prob-ability measure on the resource overflow event “ ” is
(5) where is the cumulant generating function of source . The resource overflow event is regarded as the event “
” in the analysis, and the right-hand side of (5) is the rate function that measures the set . Therefore, the outage proba-bility can be obtained by (4).
Lemma 3: The cumulant generating function of the decision
process , denoted by , is
(6) Proof: The decision process can be modeled as
, where, is 1 if and ,
other-wise. Then, can be obtained by
Similarly, the failure process from the decision
pro-cessor can be determined by . Also
is .
Lemma 4: To meet the QoS requirement of packet dropping ratio , the aggregated interference process on connec-tion is constrained by
(7) Proof: The packet dropping ratio of connection can be derived by
SHEN AND CHANG: RADIO RESOURCE INDEX FOR WCDMA CELLULAR SYSTEMS 433
Consequently, (7) can be obtained by applying the QoS
con-straint and using (8).
Proof of Theorem 1: The equivalent power generated
by each connection, , is regarded as the
equiv-alent load on the system. From the superposition property
of , the total equivalent power
should be constrained by the maximum system load , to guarantee the packet dropping ratios of all existing
connections. Define . Since
is convex and is increasing,
for and is the point in that maximizes
with . Also,
owing to the equal received power control, and
are the same for all . Additionally
(9)
where . Let be the solution
to . Since is increasing,
for all . Therefore, is the maximum point in
with the largest , and (9)
be-comes . From (7),
, and then (1) can be obtained.
Since , and by using Lemmas 1-3, the
is given by , and (2)
is obtained. If is less than the , the QoS
requirements of each connection can be guaranteed.
Equation (1) shows that the required power increment con-sists of two elements: the call level requirement-related quantity and the equivalent system
load . As the packet dropping ratio becomes
stricter, the power increment increases. Also, as the expected interference is increased, the required power increases.
IV. RESULTS ANDCONCLUSIONS
The following examines whether the packet dropping re-quirement of each connection is satisfied and the percentage of system resources is utilized when the proposed RRI is adopted for call admission control in a WCDMA cellular system. Two simulation scenarios are presented. The first scenario considers only a single traffic type with batch Poisson model (mean
rate 15 kbps and peak rate 75 kbps), dB, and
. The second scenario involves three types of traffic: Type-1 service with mean rate 15 kb/s, peak rate 75
kb/s, dB, and , Type-2 service with
mean rate 7.5 kbps, peak rate 60 kb/s, dB and
, and Type-3 service with mean rate 25 kbps, peak
rate 120 kb/s, dB, and . Also,
is set to to , and to . Note that the setting
of is the optimal case via numerical calculation based on the above given environment.
TABLE I
THEORETICAL ANDSIMULATIONRESULTS.
Table I(a) and (b) show the theoretical RRI of each connec-tion, the permission probability, , the simulated packet drop-ping ratio of connection , its QoS requirements , and the simulated maximum number of users per cell, in sce-narios 1 and 2, respectively. In scenario 1, when falls below 0.6235, the calculated RRI tends to infinity. It is because as becomes smaller, more packets suffer from excess delay and are dropped. Consequently, a higher RRI is required to reduce the channel error for fulfilling . When is set to
is smaller than . This means that the proposed RRI is too conservative in estimating the radio resources for a connection in a WCDMA system. We intensionally increase the number of connections such that approaches in the simula-tions. It is found that the maximum number of connections is 46. This indicates that the proposed RRI can reach
% utilization of system resources. In scenario
exceeds and because is loosest. Various
packet dropping ratio requirements can be met by simply allo-cating different RRIs. The RRIs calculated by (2) and (1) have a complexity that remains the same as the dimensions, such as types of services and the QoS requirements, increases, while the complexity of other conventional approaches increases with the dimensions. The RRI is a flexible mapping scheme that can transform types of connections, traffic parameters, and QoS re-quirements into the radio resource of power without increasing computational complexity.
REFERENCES
[1] L. Jorguseski, E. Fledderus, J. Farserotu, and R. Prasad, “Radio resource allocation in third-generation mobile communication systems,” IEEE Commun. Mag., vol. 39, pp. 117–123, Feb. 2001.
[2] J. Evans and D. Everitt, “Effective bandwidth-based admission control for multiservice CDMA cellular networks,” IEEE J. Select. Areas Commun., vol. 48, no. 1, pp. 36–46, Jan. 1999.
[3] 3GPP, Technical Specification Group Services and System Aspects, Working Group 2 (WG2), “QoS Concept and Architecture,” 3GPP TS 23.107, V4.1.0, June 2001.
[4] C. S. Chang and J. A. Thomas, “Effective bandwidth in high-speed dig-ital networks,” IEEE J. Select. Area Commun., vol. 13, Aug. 1995. [5] F. P. Kelly, “Effective bandwidths at multi-class queues,” Queueing Syst.,