克服組織認同衝突—網絡策略、組織認同與合作間關係之研究 - 政大學術集成
全文
(2) 誌謝 畢業了,心中充滿著感動與感激。回首過去,指導我的師長、呵護我與支 持我的家人與男友,還有那許許多多不厭其煩接受訪談與填問卷的公司主管們, 他們所給予我的感動以及點滴在心頭的感激,並不是三言兩語即可道盡。 首先,我要謝謝我的指導教授 于卓民老師。從碩士到博士,每當我需要幫 忙時,他總是伸出援手,我受過他的恩惠實在太多,在我心中他始終是個盡心盡 力愛護學生的師長。從初入博士班閱讀理論發展之經典文獻,到給我資料讓我得 以在國際會議上初試啼聲,再到解答我在研究上所碰到的各種疑難雜症以及用心. 政 治 大 之奧妙,更是個扮演好「傳道、授業、解惑」的良師典範。如果我能夠為社會貢 立. 修改我所寫的文章使其能更臻完美。這一路上,于老師不但帶領我一窺學術殿堂. ‧ 國. 學. 獻一點知識或是盡一己棉薄之力,老師的教導功不可沒。. 再來,我要感謝在美國賓州州立大學任教的 蔡文彬老師。在他所開授的社. ‧. 會網絡課程中,我不但對社會網絡理論以及相關的統計分析方法與軟體更加熟. sit. y. Nat. 悉,更學到了老師認真教學的敬業態度以及追求創新的思考方式。在與他共同合. al. er. io. 作的過程中,我真的學到非常多,從該如找到有趣的研究議題,到具有創意的思. v. n. 考,再到指正我所犯的錯誤,每回跟老師討論,都有種入寶山滿載而歸之感。他. Ch. engchi. i n U. 幫助我跳脫制式的框架,從不同的面向去看事情,嘗試想到不一樣且具有創意的 答案,這樣的思維訓練讓我一輩子受用。 接續,我要感謝我的口試委員們。謝謝 吳齊殷老師,在過去兩年修習老師 所開的社會網絡課程中,他幫助我從完全不了解社會網絡,到了解甚至喜歡上網 絡理論,謝謝老師點燃我對於社會網絡研究的濃厚興趣,也謝謝老師在博士論文 的口試中總是幫我想如何讓這份研究更有理論與實務貢獻。謝謝 王思峰老師, 仔細閱讀我的論文且毫無保留的分享他的想法,還教導我如何從不一樣的角度去 重新檢視我的個案資料。謝謝 莊璦嘉老師,在我的新構念發展不出量表之際, 給了我許多參考文章與可著手的方向,更在我茫然無助時,告訴我可以用甚麼統 2.
(3) 計方法與軟體完成這份研究,她總能在適當的時候像盞明燈指引一條出路。謝謝 蔡維奇老師,給予我紮實的研究方法課程訓練,甚至不管我在國內還是在國外, 如有問題寫信給老師,老師總能給我即時的回覆與解決方法,在口試中更樂於分 享他的研究經驗並告訴我該怎麼做。謝謝 吳秉恩老師,像個慈父永遠笑臉迎人, 在口試緊張的過程中給我安定的力量,更在論文的撰寫上教導我該如何補強。謝 謝 陳厚銘老師,從理論到方法再到衡量,都給予我許多寶貴且值得進一步思考 的建議。謝謝 巫立宇老師,在我需要幫忙且時間急迫下,幫了我一個大忙。 此外,我要感謝政大企管所內許多的師長,在我就讀碩士與博士時期給予. 治 政 大 的給予我完整的理論架構讓我的研究得以順利進行。謝謝博士期間教導我的許士 立 指導。謝謝 司徒達賢老師,訓練我在理論與實務上的反覆思考能力,並且適時. 軍老師、吳思華老師、邱志聖老師、林淑姬老師等,以及碩士期間教導我的林月. ‧ 國. 學. 雲老師、樓永堅老師、賴士葆老師、黃秉德老師、楊子江老師、陳隆麒老師等,. ‧. 他們無私的指導讓我對於企業管理的各個面向都有更深入的了解。. y. Nat. 還有,我要感謝接受訪談與幫忙填寫問卷的主管們。由於不能公佈實際公. er. io. sit. 司名稱且必須採取匿名之因,我無法在此一一將他們列舉出來,但是真的很感謝 他們在公務繁忙之際,仍願意撥空接受我的訪談,甚至不厭其煩的幫助我與找相. al. n. v i n 關人員填寫問卷。他們的協助讓我順利完成論文資料的蒐集,也對實際的企業運 Ch engchi U. 作有更深刻的體會。他們所給予我的感動與感恩,是很難用一句”謝謝你”所能表 達,但願在我的努力下,能夠有一些對實務有所貢獻的發現,好好報答這些長官 們對我的關愛與協助。 最後,我要謝謝我的家人,為了此博士論文的資料蒐集,幾乎是動員了全 家,真的很謝謝伯父與爸爸,不畏艱難也要力挺到底的幫我完成資料的蒐集,謝 謝媽媽陪我東奔西跑還有悉心的照顧我,謝謝弟弟、伯伯、叔叔、舅舅與阿姨等 的關心,還要謝謝男友,花了好幾年的時間等我畢業,且在這等待的期間中總是 給予我支持下去的力量與溫暖。家人與男友無私的付出,真的讓我很感動與常懷 3.
(4) 感恩之心。 飲水思源,如果沒有上述這麼多人的幫忙,我想我是很難順利取得博士學 位。我想對我的恩師、幫助我的許多長官們以及口試委員,還有我所愛的家人與 男友說:「謝謝你們!!真的很謝謝你們在我最需要幫忙的時候伸出援手,在我挫 折與難過時陪伴左右,我會將這份感動與感恩珍藏心中,但願有一天也能夠有所 回饋!!」. 吳紹慈 謹識於高雄. 立. 政 治 大. 2010 年 6 月 14 日. ‧. ‧ 國. 學. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. 4.
(5) OVERCOMING ORGANIZATIONAL IDENTITY CONFLICTS – THE RELATIONSHIP AMONG NETWORK STRATEGY, ORGANIZATIONAL IDENTITY, AND COOPERATION. ABSTRACT. Extant studies 政 治 大 emphasize the consequences of identity conflicts but not how conflicting parties 立. Identity conflicts can seriously endanger an organization’s survival.. extricate themselves from this trap. I investigate how an acquired firm uses network. ‧ 國. 學. strategies to develop more integrating values and distinctive values, resolve identity. ‧. conflicts, and successfully integrate into the group. To echo these qualitative. sit. y. Nat. findings, in my empirical study in the setting of a business group, I found that firms. io. cooperate with other group members.. al. er. with high identity integration and high identity differentiation have more chances to In addition, peripheral brokers are more likely. n. v i n C hand high identity differentiation, to achieve high identity integration and further have engchi U more cooperation.. Implications and future research directions are also provided.. Keywords: Network Strategy, Organizational Identity, Cooperation, Business Groups. 5.
(6) 克服組織認同衝突—網絡策略、組織認同與合作間關係之研究. 摘要. 組織認同衝突嚴重影響著組織的生存。可惜的是,過去研究多著重於探討組織認 同衝突所帶來的影響與嚴重性,但卻較少提及衝突雙方該如何解決此問題。在本. 政 治 大. 論文中,我觀察一個被購併進集團的公司,如何運用網絡策略去培養更多與集團. 立. 內其他成員相容的價值,同時保存與發展了獨特的價值,進而幫助個案公司跳脫. ‧ 國. 學. 認同衝突的困境並成功整合進集團。為了呼應個案研究之發現,我以一個集團企 業做為研究情境,搜集資料並進行實證研究,我發現當一家公司同時具備高整合. ‧. 與高差異化的組織認同時,可得到較多與集團內其他成員合作的機會。此外,在. y. Nat. sit. 集團網絡中佔據邊陲掮客網絡位置的成員,較有可能培養出高整合與高差異化之. n. al. er. io. 組織認同,進而得到較多的合作。本論文亦於結尾提供研究意涵與未來研究方向。. Ch. engchi. 關鍵字: 網絡策略, 組織認同, 合作, 集團企業. i n U. v. 6.
(7) CONTENTS. OVERCOMING ORGANIZATIONAL IDENTITY CONFLICTS – THE RELATIONSHIP AMONG NETWORK STRATEGY, ORGANIZATIONAL IDENTITY, AND COOPERATION. CHAPTER 1: INTRODUCTION Section 1.1: RESEARCH GAP AND RESEARCH QUESTION. 政 治 大 Section 1.3: BRIEF OUTLINE 立 OF THE THESIS Section 1.2: RESEARCH PROCESS. 12 13. ‧ 國. 學. CHAPTER 2: LITERATURE REVIEW. 10. 15. ‧. 21. y. 28. sit. CHAPTER 3: CASE STUDY. 62. Section 3.1: DATA COLLECTION. Nat. Section 3.2: FINDINGS. n. al. CHAPTER 5: RESEARCH METHODOLOGY. Ch. engchi. er. io. CHAPTER 4: HYPOTHESES. i n U. v. Section 5.1: RESEARCH SITE AND DATA COLLECTION. 69. Section 5.2: MEASURES. 72. CHAPTER 6: EMPIRICAL RESULTS. 88. CHAPTER 7: DISCUSSION AND CONCLUSION Section 7.1: DISCUSSION AND RESEARCH CONTRIBUTIONS. 96. Section 7.2: MANAGERIAL IMPLICATIONS. 100. Section 7.3: RESEARCH LIMITATIONS AND FUTURE RESEARCH. 102. DIRECTIONS REFERENCES. 104 7.
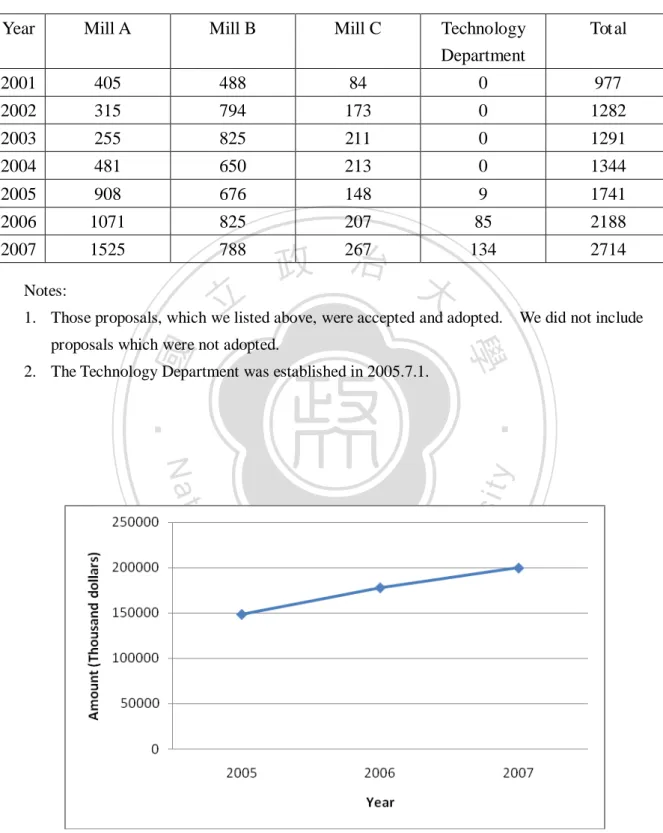
(8) TABLES. TABLE 3.1、DATA COLLECTION FOR CASE STUDY. 22. TABLE 3.2、SUMMARY OF PARTICIPANTS INTERVIEWED. 24. 政 治 大. TABLE 3.3、IDENTITY CONFLICTS BETWEEN BETA GROUP AND BA CO. 30 TABLE 3.4、CO-EVOLUTION. 立. 47. TABLE 3.5、THE TOTAL NUMBER OF PROPOSALS FOR IMPROVEMENT 48. ‧ 國. 學. (2001-2007). 49. TABLE 3.7、BA CO.’s DISTINCTIVE IDENTITIES. 54. ‧. TABLE 3.6、CUSTOMERS’ PERCEPTIONS CHANGES IN BA CO.. sit. y. Nat. io. er. TABLE 5.1、DATA COLLECTION FOR EMPIRICAL STUDY. TABLE 5.2、SUMMARY OF DIMENSIONS AND MEASURES. n. al. Ch. n U engchi. iv. 71 78. TABLE 5.3、FACTOR ANALYSIS FOR IDENTITY DIFFERENTIATION. 81. TABLE 5.4、FACTOR ANALYSIS FOR IDENTITY INTEGRATION. 83. TABLE 6.1、MEANS, STANDARD DEVIATIONS, AND CORRELATIONS. 92. TABLE 6.2、RESULTS OF POLYNOMIAL REGRESSION: COOPERATION. 93. TABLE 6.3、RESULTS OF BINARY LOGISTIC MODEL: HIGH IDENTITY. 93. INTEGRATION AND HIGH IDENTITY DIFFERENTIATION TABLE 6.4、RESULTS OF HIERARCHICAL REGRESSION: COOPERATION 94. 8.
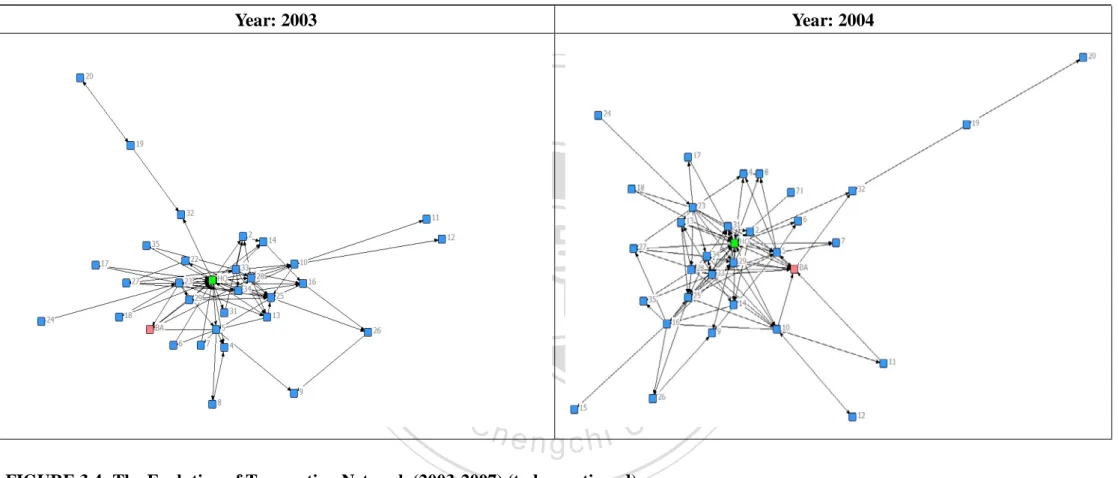
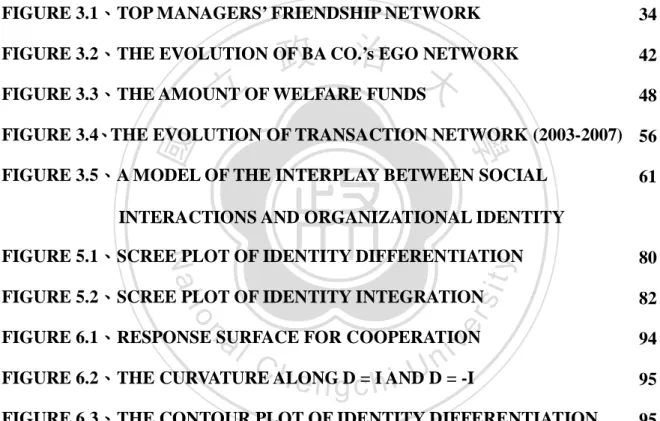
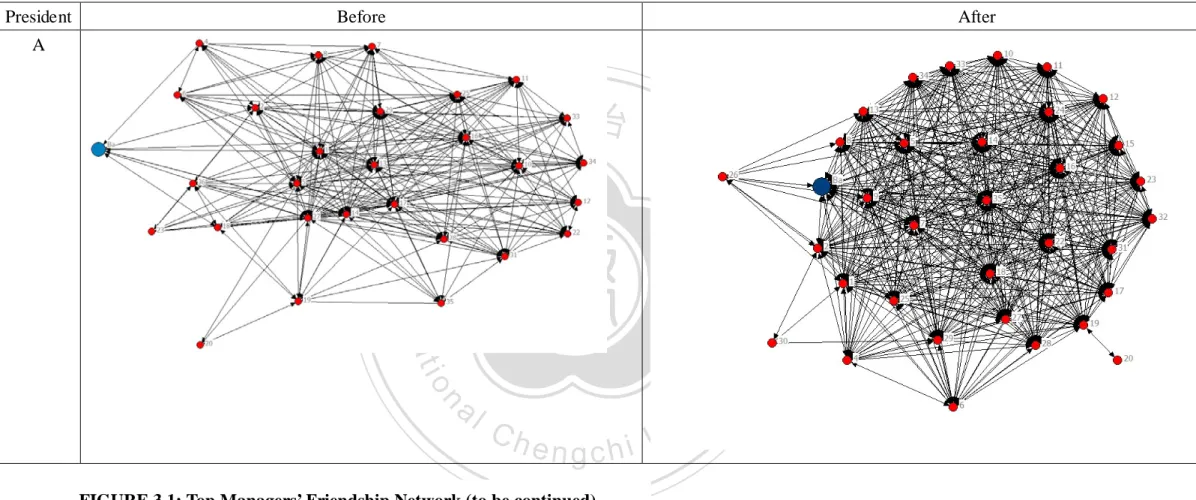
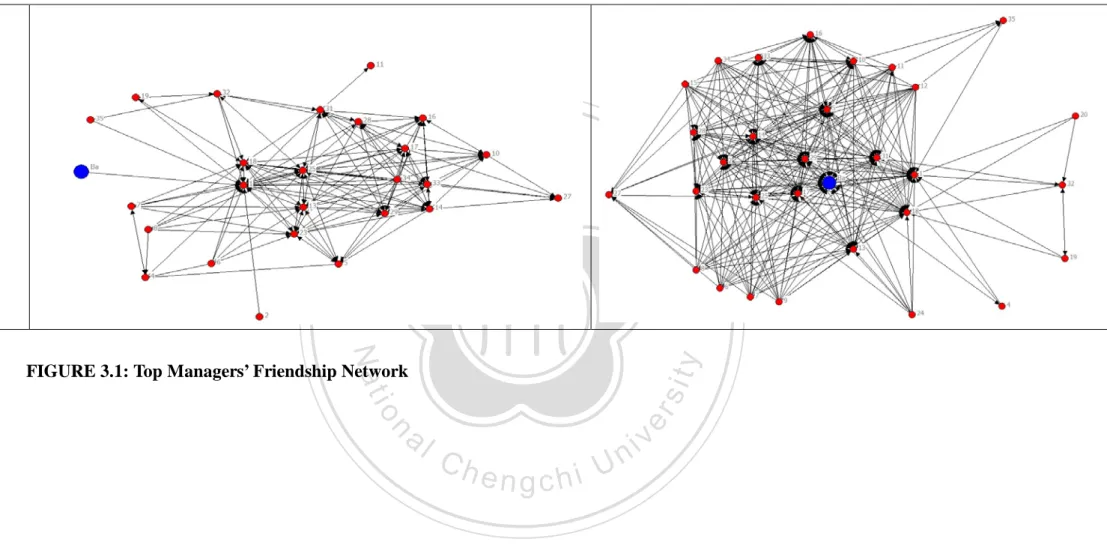
(9) FIGURES. FIGURE 3.1、TOP MANAGERS’ FRIENDSHIP NETWORK. 34. 政 治 大 FIGURE 3.3、THE AMOUNT 立OF WELFARE FUNDS. FIGURE 3.2、THE EVOLUTION OF BA CO.’s EGO NETWORK. 42 48. ‧ 國. 學. FIGURE 3.4、THE EVOLUTION OF TRANSACTION NETWORK (2003-2007) 56 FIGURE 3.5、A MODEL OF THE INTERPLAY BETWEEN SOCIAL. 61. ‧. INTERACTIONS AND ORGANIZATIONAL IDENTITY. y. 80. sit. Nat. FIGURE 5.1、SCREE PLOT OF IDENTITY DIFFERENTIATION. 82. al. er. io. FIGURE 5.2、SCREE PLOT OF IDENTITY INTEGRATION. 94. FIGURE 6.2、THE CURVATURE ALONG D = I AND D = -I. 95. FIGURE 6.3、THE CONTOUR PLOT OF IDENTITY DIFFERENTIATION. 95. n. v. FIGURE 6.1、RESPONSE SURFACE FOR COOPERATION. Ch. engchi. i n U. AND IDENTITY INTEGRATION. 9.
(10) CHAPTER 1. INTRODUCTION SECTION 1.1. RESEARCH GAP AND RESEARCH QUESTION Organizational identity theory is a cornerstone of management literature. Organizational identity represents a shared understanding of the central, distinctive, and enduring characteristics of the organization among its members (Albert & Whetten, 1985; Dutton & Dukerich, 1991).. When organizations face identity threats. which basically question insiders’ self-perceptions, the feelings of hostility are Moreover, it is not easy for conflicting 政 治 大 parties extricate themselves from this conflict trap which endangers organizations’ 立 inclined to escalate (e.g., Northrup, 1989).. survival (Fiol, Pratt, & O’Connor, 2009).. However, how do firms resolve identity. ‧ 國. 學. conflicts? Although there is considerable consensus on the importance of resolving. ‧. identity conflict, I still do not comprehend what pushes people to rethink the nature of. sit. y. Nat. their identities and further modify their identities to terminate identity conflicts.. io. explanatory variables and acquisition performance.. al. er. In the past decades, many studies empirically test the relationship between In spite of this, researchers still. n. v i n encourage future research to payCmore attention on theU h e n g c h i integration process and clarify casual ambiguity between integration decisions and outcomes (Datta & Grant, 1990; Hitt, Harrison, Ireland, & Best, 1998; Hoskisson, Hitt, Johnson, & Moesel, 1993).. As a result, I attempt to understand the strategy of a newly merged firm which faced serious identity conflicts in the post-acquisition period and had better be spun-off, but it, surprisingly, resolved identity conflicts and successfully integrated into the group. Moreover, this merged firm was a peripheral actor when it joined the business group.. After several years, it moved to a relatively central position.. How did it. achieve this goal and gain more cooperation with other group members? What kind of network position can help it to use an innovative strategy to gain more chances of 10.
(11) cooperation? I add theoretical values in four ways.. First, I explicate the long-term process. leading a new group member to transform its identities, to terminate other members’ hostility towards it, and finally to become a role model.. Second, while traditional. organizational identity literature emphasizes that increasing similarities and decreasing dissimilarities can reduce hostility among conflicting parties, I propose that increasing similarities and decreasing dissimilarities is not the only way out. Third, while traditional social network literature focused on the behavior of central. 政 治 大 can improve their positions by changing their combination of identities; this is a way 立. actors, I try to examine the strategy of peripheral actors. I find that peripheral actors. which never came into my mind and seldom be mentioned by previous studies.. ‧ 國. 學. Fourth, while existing literature argues that central actors are more likely to gain more. First, while previous. io. er. Moreover, I add methodological values in two ways.. sit. y. Nat. cooperation. ‧. cooperation, I, counter-intuitively, find that peripheral brokers can obtain more. studies cannot collect invisible and longitudinal network data in the business group. al. n. v i n C hI successfully complete due to the difficulty of data access, this task. engchi U. Second, I. combine deductive and inductive approaches to find multiple dimensions of two important constructs in the management field, integration and differentiation.. 11.
(12) SECTION 1.2. RESEARCH PROCESS This study includes three stages.. In the initial stage, I went through. organizational identity and social network literature, looking for possible and valuable research issues.. Meanwhile, I chose a business group which is among the world’s. Top 20 largest firms in mental industry as my research setting and spent five months to interview top managers and visited many group affiliates.. I finally discovered an. interesting case and some potential research questions. In the second stage, I collected interview and various kinds of self-report data. 政 治 大 Then,立 I not only developed theoretical hypotheses but also. and secondary data to complete case study which interprets an integration process of a newly merged firm.. ‧ 國. 學. combined deductive and inductive ways to generate items for two new constructs, identity integration and identity differentiation.. Regarding other variables, I picked. ‧. out measures which were reliable and validated in previous studies.. sit. y. Nat. In the third stage, I collected data from multiple sources to test my hypotheses.. n. al. Theoretical. er. io. The insights from case study were verified by the empirical findings.. i n U. v. and practical implications and directions of future research are offered.. Ch. engchi. 12.
(13) SECTION 1.3. BRIEF OUTLINE OF THE THESIS This thesis is structured as follows: CHAPTER 1. INTRODUCTION: Research gap, research question, research process, and brief outline of the thesis are illustrated in this chapter. CHAPTER 2. LITERATURE REVIEW: In the beginning, the definition of organizational identity is provided and the importance of resolving identity conflict is stressed.. If conflicting parties would like to extricate themselves from conflict trap,. they might need to modify or change their identities.. In order to know identity. 政 治 大 reason why organizational 立 identity changes can occur. More recently, scholars have. changes, I trace the history of organizational identity literature, which offers the. ‧ 國. 學. moved on to the question of how organizational identity changes can occur. Although the serious consequences of identity conflicts are commonly mentioned,. ‧. existing studies seldom provide some evidence and illustrate what kind of network. y. sit. n. al. er. In the end of this chapter, I briefly explain why I choose an acquired. io. conflict trap.. Nat. strategy can guide network actors to change their identities and get out of the identity. i n U. v. firm as research target and conduct case study to know the change process.. Ch. engchi. CHAPTER 3. CASE STUDY: I discuss data sources and data collection methods first. Then, I report longitudinal research on the process leading a merged firm to reach identity integration and identity differentiation, to successfully integrate into a business group, and to further become a role model in the third chapter. CHAPTER 4. HYPOTHESES: To verify the findings in the case study, I also conduct an empirical stud y.. When I develop hypotheses, I not only deductively. develop some theoretical arguments but also propose some new ideas. CHAPTER 5. RESEARCH METHODOLOGY: I discuss data sources, data collection methods, measures, and related information (such as validity, reliability, 13.
(14) and data aggregation) in the fifth chapter. CHAPTER 6. EMPIRICAL RESULTS: I start with descriptive statistics and correlations for all measured variables.. Then, I present detailed information about. the results of empirical testing. CHAPTER 7. DISCUSSION AND CONCLUSION: I summarize major findings to echo our research question and research purposes, discuss the implications, and provide directions of future research in the seventh chapter.. 立. 政 治 大. ‧. ‧ 國. 學. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. 14.
(15) CHAPTER 2. LITERATURE REVIEW Organizational identity represents the members’ collective beliefs about what is the central, distinctive, and enduring essence of the organization (Albert & Whetten, 1985; Dutton & Dukerich, 1991).. Every organization needs the identity to. differentiate it from others and to help insiders to answer the question about who they are as an organization (Albert & Whetten, 1985; Ashforth & Mael, 1996). an organization does not automatically announce its identity.. However,. Rather, internal. stakeholders’ perception, attention, and interpretation come together to define “what There is 政 治 大 recognition that organizational 立 identity reflects not only how people categorize does this organization stand for?” and distinguish themselves from others.. ‧ 國. 學. themselves (Ashforth & Mael, 1989; Rao, Davis, & Ward, 2000) but also how people perceive the world.. Unfortunately, people tend to pick out those bits of information. ‧. that make they feel good because those pieces of information confirm their beliefs This signifies that an organization will suffer through members’. sit. y. Nat. (Northrup, 1989).. n. al. er. io. refusal to accept identity change, even though it is a beneficial change, because. i n U. v. members prefer to believe that their belief is the best for the organization (Reger,. Ch. engchi. Gustafson, DeMarie, & Mullane, 1994) and avoid the perceived world is disrupted. Scholars have noted that the identity change process may last for a long period of time (eg., Albert & Whetten, 1985).. Fully understanding the difficulty of identity change,. it is not hard to comprehend that, when organizations face threats to their identities, conflicts go worse, because those threats fundamentally challenge insiders’ self-definitions and question their own beliefs (e.g., Northrup, 1989).. This cognitive. dissonance could cause one side or other to escalate the conflict. To the best of my knowledge, however, the literature provides little evidence to explicate successful changes of organizational identity.. Numerous researchers have placed primary 15.
(16) emphasis on the antecedents of or the outcomes of organizational identity, with little emphasis on organizational identity itself and investigating how an organization find ways to change its identity and get out of an identity conflict trap (e.g., Corley & Gioia, 2004; Fiol, Pratt, & O’Connor, 2009; Ravasi & Schultz, 2006). According to social identity theory, actors incline to classify themselves and others into different categories (Tajfel & Turner, 1985).. The suitable and keenly. anticipated behavior gives meaning to the category (Rao, Davis, & Ward, 2000) and draws a boundary between “us” and “them”.. To avoid the boundary being blurred. 政 治 大 dissimilarities between groups (Rao, Davis, & Ward, 2000). 立. and muddled, people tend to highlight the similarities within groups and Sometimes members. build their self-definitions on defining who they are not (disidentification) (Dukerich,. ‧ 國. 學. Kramer, & Parks, 1998; Elsbach, 1999; Pratt, 2000) or looking down on others (Rao,. ‧. Davis, & Ward, 2000) to accentuate the group to which they belong is better than. sit. y. Nat. other groups. The negation of others makes it difficult for people to stop viewing. io. er. others as the enemy, because the feelings of hostility toward one another come from denying a central or large element of other group’s identity (Ashmore, Jussim, Wilder,. al. n. v i n C h As for the focal group, & Heppen, 2001; Northrup, 1989). an agreement with other engchi U. group’s identity is directly or indirectly against their own identity which is established on negatively stereotyping others.. When identity is involved in a conflict, such. long-lasting conflict traps the organization in a spiral trend of disharmony and endangers the organization’s survival (Fiol, Pratt, & O’Connor, 2009). considerable consensus on the importance of resolving identity conflict.. There is While. researchers propose what is needed is a change of identity to extricate conflicting parties from the conflict trap (Kelman, 2006; Northrup, 1989), I am still left in the dark about what pushes people to rethink the nature of their identities as well as making further changes and how to terminate the identity conflict. 16.
(17) Dutton and Dukerich(1991), studying how the Port Authority of New York/New Jersey adapted to environmental shift, offered an early description of the effect of organizational identity on members’ perception as well as organizational action. Their findings showed that organizational identities and insiders’ awareness of what outsiders think about the organization jointly determined members’ interpretations of an issue and organizational changes.. When insiders were aware that there is a gap. between their own perceptions and outsiders’ perceptions of the organization, they will re-examine both their understanding of “what does this organization mean?” and Reger et al.(1994) further proposed a 政 治 大 dynamic framework in which leaders’ reframing abilities can guide the evolution of 立 their membership of this organization.. organizational identity by constructing an ideal identity.. The perceived gap between. ‧ 國. 學. current (“who we are”) and ideal identity (“who we want to be”) pushes members to To provide empirical evidence of. ‧. have a mind to transform organizational identities.. sit. y. Nat. the relationship between identity gap and identity change, Gioia and Thomas(1996). io. existing identities to reach possible selves.. al. er. looked into how top management teams in a large public research university unfroze Their findings that desired future image. n. v i n C h identity transformation. acted as the trigger for organizational engchi U. Similarly, the. discrepancies between insiders’ self-definitions (the identity) and outsiders’ feedback set off organizational identity shifts (Elsbach & Kramer, 1996; Foreman & Whetten, 2002; Gioia, Schultz, & Corley, 2000).. Tracing the history of organizational identity. literature, I can gradually realize the reason why organizational identity changes can occur. More recently, identity researchers have moved on to the question of how organizational identity changes can occur.. Fiol(2002) argued that rhetorical. techniques are important tools for executives to loosen members’ ties with old identities and tighten members’ ties with new core values, for the sake of relieving the 17.
(18) pressure of resistance during times of identity changes.. Similar to rhetorical. techniques, identity ambiguity (members have no clear sense of “who they are”) opens the space for reframing perceptions of identity (Corley & Gioia, 2004). To interpret how a group can change its identity and further extricate itself from an identity conflict trap, Fiol, Pratt, & O’Connor (2009) presented an intractable identity conflict model that the validation of subgroups’ identities provides a secure place for subgroup members and creates subgroup members’ willingness to adopt a dual identity which contributes to intergroup harmony.. However, organizations are. 政 治 大 Rather, organizations have to trade with each other and interact with other 立. unable to create a self-sufficient world for themselves or isolate themselves from all society.. entities (e.g., Freeman, 1984; Granovetter, 1985; Uzzi, 1997; Rao, Davis, & Ward,. ‧ 國. 學. 2000).. While existing studies focus on one party’s identity which is contingent on. ‧. the focal party’s perception (“who do I think I stand for?”) and the other party’s. sit. y. Nat. feedback (“who do they think I stand for?”), they neglect that, through social. io. er. interaction, the other party’s perception may also be influenced by the focal party and such perception shift determines how they make sense of the focal party.. al. n. v i n C h that social interaction Conventional wisdom suggests shapes actors’ identities engchi U. (e.g., Cooley, 1902; Goffman, 1959; Ibarra, Kilduff, & Tsai, 2005; Mead, 1934; White, 1992). To illustrate, Becker and Carper (1956) observed that, through social interaction, graduate students in physiology gradually shifted their attitudes to “who they are” from “who they want to gain admissions from medical schools and regard the physiology department as a stopgap” to physiologists. peers molded students’ values, norms, and self-definitions.. Frequent interaction with Using a network of. partners, people distribute messages “who they are” or “who they want to be seen” to others (Ibarra, 1999).. By observing partners’ response to their messages, people. keep or modify their identities (Swann, 1987).. As a result, identities have been 18.
(19) viewed as outcomes of negotiation between different parties in social networks (e.g., Cooley, 1902; Mead, 1934; Goffman, 1959).. Nevertheless, the effect of one party’s. reactions on the other party’s identities is not one way only. each other reciprocally and simultaneously.. Both sides influence. While the focal actor modifies its. self-conceptions due to the awareness of the discrepancies between its perceptions and others’ feedback, meanwhile, other actors, influenced by the focal one, also modify their perceptions toward the focal actor or even redefine their self-conceptions. It is thus evident that networks pour dynamic elements into the identity transformation Actors prefer to build connections with 政 治 大 people who can help find possible selves but simultaneously abandon connections 立 process (Ibarra, Kilduff, & Tsai, 2005).. with people who can limit the improvement of identities (Ibarra, Kilduff, & Tsai,. ‧ 國. 學. 2005).. Although the association between social interaction and identity is well. ‧. documented, I have limited empirical evidence about how one’s relations with others. sit. y. Nat. serve as the fountainhead of organizational identity shifts (Brickson, 2005).. io. er. Moreover, while existing works try to provide a satisfactory explanation for why and how a focal actor can extricate itself from identity conflict trap, I try to provide more. al. n. v i n C hin the identity conflict empirical suppo rt (which is limited literature) to explicate why engchi U and how a newcomer can use networking strategy to change its identities, to further shift others’ perceptions towards it and themselves, and to reach harmony. Because the identity literature seldom examines how social interaction facilitates a firm’s abilities to trigger identity changes and to free conflicting parties from identity conflict trap, I undertook the investigation inductively, adopting an interpretive approach.. Interpretive approach can help me build theoretical arguments. by inferring from what people (who were there during times of identity conflict and experiencing the transition) said and what archival data showed.. Unfortunately, it is. difficult to observe the evolution of organizational identity or prompt insiders to share 19.
(20) experiences, because insiders incline to keep silence to maintain the stability of their identities (Whetten & Godfrey, 1998).. For this reason, I chose a research context in. which the issue of identity conflict (which was reported in the newspapers) was obvious to make insiders feel more comfortable to talk about this transition. successful integration case was chosen by me for this case study.. A. Compared to other. members, the newcomer I studied initially had widely different identities which made it had better be spun off; however, it has successfully integrated into the group. This case study reports longitudinal research on the process leading this newcomer to. 政 治 大 The case study is followed by an empirical study. 立. transform its identities, to terminate other members’ hostility towards it, and finally to become a role model.. I collected. long-term data from multiple sources to echo findings in the case study.. ‧. ‧ 國. 學. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. 20.
(21) CHAPTER 3. CASE STUDY SECTION 3.1. DATA COLLECTION The organization I studied was acquired by a large and multinational business group (fictitious name: BETA Group) in 2000.. At the time of acquisition, BETA Co.. (the group headquarters) obtained the ownership of the acquired organization (which was given a fictitious name “Ba Co.”) in terms of equity holdings and had the power to determine board positions.. Unfortunately, other group members refused to accept. 政 治 大 accordance with legal requirements or group boundaries defined by numerous 立 Ba Co. as one of them, even though it had the membership of BETA Group in. scholars (e.g., Granovetter, 1995; Khanna & Rivkin, 2001).. On the other hand,. ‧ 國. 學. people in Ba Co. felt frustrated and confused due to this gap and the hostility towards In the initial stage, Ba Co. was considered an unwelcome isolator within the Going through a tough time, Ba Co. was gradually accepted by other. sit. y. Nat. group.. ‧. them.. io. n. al. er. members and eventually became a role model.. Data Collection. Ch. engchi. i n U. v. To avoid any problems owing to retrospective data (e.g., post-event rationalizations), I corroborate informants’ accounts by different informants’ statements or alternative sources.. As a result, I collected not only interview data but. also self-report data and archival data.. All data collection was longitudinal.. The. interview data combined historical data and current data collected during the research period.. The self-report data covers the period 2001-2007.. The archival data spans. 9 years, from the announcement of acquisition to the end of this research project (2000-2008). Table 3.1 lists all kinds of data, time period, and data sources.. 21.
(22) Tab le 3.1 Data Collection for Case Study Data. Time Period. Interview Data. Historical and current data. Data Sources 1. Formal interview: 26 semi-structured interviews. 220 pages of written transcriptions. 2. Informal interview. Self-report Data 1. Transaction Network. 2001-2007. All group members: 2003-2007.. Ba. Co.: 2001-2007.. 2. Personnel Transfer. 2001-2007. All group members: 2003-2007.. Ba. Co.: 2001-2007.. Network 2001 and 2007. 立. 2000-2008. 2. Excellent Business Database System (EBDS) 3. Business Groups in Taiwan compiled by CCIS. ‧. 4. Tsai Hsun (Wealth Magazine) Database 5. Biographies, corporate annual reports, and books.. io. sit. y. Nat. Interview data.. 1. Internal documents (i.e., meeting memos, statistics). 學. ‧ 國. Archival Data. Three presidents 政 治 大. al. er. 3. Friendship Network. v i n perceiving some transformationsCinhan organizationi (e.g., e n g c h U Isabella, 1990). n. Researchers have indicated that top management team plays a crucial role in Their. active participation in organizational changes gets top managers to be viewed as important interviewees (Kumar, Stern, & Anderson, 1993).. As a result, I began this. research project by choosing top managers as key informants who can tell me the process of this transition.. Then, I requested these top managers to recommend. additional informants at different hierarchical levels or different functional areas.. I. conducted 26 semi-structured interviews; all were tape-recorded and transcribed, yielding close to 220 pages of written transcriptions.. To clarify differences and. discrepancies, I had multiple interviews with some participants, so twenty key 22.
(23) executives were interviewed.. Mangers from different backgrounds, different levels,. different functions, and different group affiliates who participated in or influenced by the decision of networking strategies and organizational identity changes were formally interviewed.. These interviews offered more detailed information about. how network strategies, identity conflicts, and identity changes were perceived and experienced by individuals.. Throughout the research period, informal discussion. with different employees was used to confirm the data I obtained from formal interviews.. For example, if A told me something about the routine of alpha. 政 治 大 The list of managers who were formally interviewed, their positions and the 立. department, I would ask B to describe the routine of alpha department to verify A’s words.. number of times they were interviewed is shown in Table 3.2.. ‧ 國. 學. All interviews lasted approximately three hours. I began the initial interview. ‧. with a vague research question: How did the Ba Co. successfully integrate into the. sit. y. Nat. group while conflicts between it and other group-affiliated firms were apparent at the. io. expanded the range of subsequent data collection.. al. er. beginning? The initial interview laid the foundations for subsequent interviews and The follow-up interviews were. n. v i n C hhow people did and semi-structured, for comprehending experienced this historical engchi U. transition, rather than how people thought about it. Following guidelines for. qualitative studies, I conducted the initial and follow-up interviews as descriptive as possible until the main motif, social interaction (“building connections and maintaining good relationships with sister firms” mentioned by key informants), came up (e.g., Miles & Huberman, 1994).. Subsequent interviews became more structured. and emphasized on main themes like networking strategy and the relationship between social interaction and organizational identity changes which I would like to explore in detail. 23.
(24) TABLE 3.2 Summary of Participants Interviewed Interviewees. Number of interviews. 1.President, Ba Co. 2.President, Bb Co. 3.President, Bc Co. 4.President, Bd Co. 5.President, Be Co. 6.Vice President, Production Division, Ba Co. 7.Vice President, Administration Division, Ba Co. 8.Vice President, Business Division 1, Bf Co. in 2007 9. Assistant Vice President, BETA Co. 10.Deputy General Manager, Information & System Department, Ba Co. 11.Deputy General Manager, Commercial Administration Department, Ba Co. 12. General Superintendent, Mill A, Ba Co. 13. General Superintendent, Mill B, Ba Co. 14. Assistant General Superintendent, Mill B, BETA Co. 15. Consultant, Ba Co. in 2003-2007 16.Senior Manager, Production Division, BETA Co 17.Senior Manager, Business Division 1, Bf Co. 18.Senior Manager, Business Division 2, Bf Co. 19.Senior Manager, Commercial Division, Bg Co. 20.Senior Manager, Administration Division, Bg Co.. 立. 4 2 2 1 1 1 1 1 1 1 1 1 1 1 1 2 1 1 1 1. 政 治 大. ‧. ‧ 國. 學. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. Self-report data. To confirm informants’ accounts and examine inter-firm linkages within the group, I gathered longitudinal network data through surveys. Transaction network and personnel transfer network To outline the evolution of network, I used sociometric techniques to collect long-term information about transaction network and personnel transfer network. The data of both networks were historical, covering the period 2003-2007.. I. distributed these network surveys to all companies in the BETA Group. To verify 24.
(25) the responses, I also asked opposite questions.. For transaction network, I asked the. focal firm to indicate sister affiliates which sell products or services to it.. For. personnel transfer network, I requested the focal firm to identify sister affiliates which transfer talents to it to act as managers.. To validate the data, I also asked opposite. questions, “which group members buy products or services from you” and “which group members transfer managers from your firm”.. I offered a list of all group. members in the questionnaire so that respondents can easily choose their answers from the list.. In addition, I double-checked all answers; for example, when firm i. 政 治 大 product or service buyer, an transaction relationship was recognized. 立. pointed out firm j as a product or service provider and firm j pointed out firm i as a I did follow-up. interviews (i.e., interviewing managers in firm i and firm j) to clarify some. ‧ 國. 學. discrepancies.. I further asked the Ba Co. to offer information about transaction and. ‧. personnel transfer network during the period 2001-2002; these documents enabled me. sit. y. Nat. to grasp its ego network evolution.. n. al. er. io. Executives’ friendship network. i n U. v. Because executives’ friends affect executives’ cognitions which shape firms’. Ch. engchi. strategic responses (McDonald & Westphal, 2003), I also use a questionnaire to sketch the outline of 2001(the next year after the acquisition) and 2007(the time I collected friendship data) top executives’ (the boss and the president of each group-affiliated firms) friendships within the group.. I listed the names of all. chairmans and presidents in the group and initially asked the president of the Ba Co. (who was assigned to be an executive in the Ba Co. in the initial stage of post-acquisition and experienced throughout the transformation period) to indicate whom was who’s friend in 2001 and in 2007.. The BETA Group had 29 group. members in 2001 and 35 group members in 2007.. As a result, based on the 25.
(26) president’s answers, I was able to create a 29×29 top managers’ friendship matrix for 2001 and a 35×35 matrix for 2007. These friendship matrices are cognitive maps which represent an individual’s perceptions of who links to whom in a particular social system (Kilduff & Tsai, 2003).. However, there is a gap between how people. perceive this network and the actual pattern of connections existing in this network. In another word, people have biases in social perceptions (Kilduff & Krackhardt, 1994; Kumbasar, Romney, & Batchelder, 1994). For the sake of reducing biases, I chose another two presidents (one from a central firm and the other from a peripheral firm) to fill out this questionnaire.. 立. Archival data.. 政 治 大. ‧ 國. 學. To investigate the process of resolving identity conflict and understand the thought behind it, I collected a wide scope of information.. First, the main source. ‧. These archival data helped me to illustrate the. io. sit. Nat. functional areas within the Ba Co.. y. was different kinds of documents (i.e., meeting memos, statistics) collected from all. n. al. er. evolution of organizational identities and understand the response from outsiders,. i n U. v. including the headquarters of BETA Group, other group-affiliated firms, and external. Ch. stakeholders such as customers.. engchi. The second source was the Excellent Business. Database System (EBDS), an electronic database, providing full-text of more than 200 periodicals and newspapers published in Taiwan.. The third one was the. directory of Business Groups in Taiwan which is compiled by the China Credit Information Service (CCIS), an affiliate of Standard & Poor of the United States and the most prestigious credit checking agency in Taiwan.. Since 1972, the China Credit. Information Service (CCIS) has compiled more than 6,000 individual companies from nearly 300 groups for Business Groups in Taiwan.. This directory has become the. most complete source for business groups in Taiwan and has been widely used in 26.
(27) previous literatures (e.g., Luo & Chung, 2005; Khanna & Rivkin, 2001).. For each. group, this directory contains not only the history of groups’ growth but also various financial analyses of group-affiliated firms.. Fourth, I referred to Tsai Hsun (Wealth. Magazine) database which has periodical articles about large business groups in Taiwan.. Fifth, I surveyed biographies, corporate annual reports, and books that were. related to this topic.. 立. 政 治 大. ‧. ‧ 國. 學. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. 27.
(28) SECTION 3.2. FINDINGS The initial stage of post-acquisition: Identity conflicts and the paucity of contacts Originally, Ba Co. was a member of Alpha Group. Until 2000, Ba Co. did not increase the volume of production and its liabilities went up to $5 billion (U.S. dollars) (Hsu, 2000).. The leader of Alpha Group could not stand its continued losses, so he. decided to sell it to the BETA Group.. When the boss of BETA Group announced the. acquisition of Ba Co., he faced a wave of opposition which mainly came from BETA Co.’s labor union (Liu, 2002; Wong, 2002).. The blast showed the depth of worry. 政 治 大 a financial burden on them立 but also a wide gap between the buyer and the target.. among group members over negative effects of this acquisition, including not merely For. ‧ 國. 學. example, Ba Co. had a bad reputation in the market because it was used to breach a contract to maximize its profits.. One executive noted:. ‧. When the market price went up, our boss [at that time] would request customers to raise the price.. If. y. As for him (the boss of Ba Co.), our company did not violate the [transaction]. sit. refuse to sell goods.. Nat. they (customers) insisted on buying our products with the same price noted on the contract, he would. n. al. er. io. contract because he did inform customers to raise the price before he refused to sell goods.. i n U. v. Conversely, BETA Group stood as a model group of trustworthy (Wu, 1997).. Ch. engchi. president of one group-affiliated firm stated:. A vice. The year 2000 was a period of economic recession. I [remembered that I] signed a contract to buy some raw materials from a supplier in Russia. After a week, the exchange rate changed; the change went beyond my imagination. Although I knew the deal would lead to a huge amount of losses, I still executed the contract.. At that time, I was in China.. I roamed around China for several months and. did not have the courage to go home because I felt very sorry for my fellows.. The significant differences between the attitudes toward trustworthy of both sides just revealed the tip of the iceberg.. Table 3.3 summarized varied dimensions of identity. and examples to show how Ba Co.’s actions were far away from or even contradicted BETA Group’s actions.. Reminiscing about his reaction to the news of acquisition, 28.
(29) one senior manager of BETA Co. noted: [For instance,] We could borrow funds from banks with extremely low interest rates. Sometimes bankers actively [knocked our doors and] asked us whether we could borrow some money from them. They (those bankers) were not fools; they were willing to do so because of the name of our company. The name embroidered on here (our uniforms) and printed on [our] business cards represented trustworthiness. They (the bankers) never have a doubt about whether our company would [follow the contract to] give the money back. bankers refused to lend the money.. Me either.. [On the contrary,] Ba Co. was a firm to which. I didn’t understand why our boss would like to acquire such a. compa ny.. The example is illustrative of a serious problem that group members were confused. 政 治 大 conform to or contradict the salient part of their identities. 立. and refused to accept a newcomer when they were aware that the newcomer did not Those conflicting beliefs. or actions gradually and imperceptibly drew a clear line between “us” and “them”.. ‧ 國. 學. In the primary stage of post-acquisition, Ba Co. had few links with members of One executive recalled: “We had no connections with group members. Except friendships. sit. y. Nat. I knew our boss and the leader of the group were good friends.. ‧. BETA Group.. io. er. between them, we had very few, nearly no, links with the group headquarters or other members [in BETA Group].” The paucity of contacts resulted in Ba Co. being. al. n. v i n C h of “us”, becauseUlack of a contact resulted in viewed as anything but not a member engchi lack of a feeling of membership.. Besides, group members made sense of “what does. Ba Co. stand for” by observing the portfolio of its partners.. One president of a. group-affiliated firm told us: Its boss (the boss of Ba Co.) came from Alpha Group.. Although the group headquarters (BETA Co.). assigned the boss and had a stake in it (Ba Co.), ownership could not represent membership; they (Ba Co.) still belonged to Alpha Group. … because it was still difficult for us to obtain some orders from Ba Co.. They (Ba Co.) still traded with those people (original suppliers) and they did not back me up. as a family.. 29.
(30) TABLE 3.3 Identity Conflicts between BETA Group and Ba Co.. 立. y. sit. n. al. er. io. Respect for people Flexibility. Ba Co.. ‧. Nat. Institutionalization. 政 治 大. Interview: “The year 2000 was a period of economic recession. I Interview: “When the market price went up, our boss [at that time] would [remembered that I] signed a contract to buy some raw materials from a request customers to raise the price. If they (customers) insisted on supplier in Russia. After a week, the exchange rate changed; the buying our products with the same price noted on the contract, he would change went beyond my imagination. Although I knew the deal would refuse to sell goods. As for him (the boss of Ba Co.), our company did lead to a huge amount of losses, I still executed the contract. At that not violate the [transaction] contract because he did inform customers to time, I was in China. I roamed around China for several months and raise the price before he refused to sell goods.” did not have the courage to go home because I felt very sorry for my fellows.” Interview: “[Previously,] I just did what the boss [of Alpha Group] asked us to do. He is always right. [Therefore,] technicians in Ba Co. were used to obey their superiors’ commands. …[However, in BETA Co.,] managers were used to let subordinates make detailed plans. …[Thus,] when they came to Ba Co. and acted as top managers, there was a gap between us. They expected us to work out some plans, [but] I expected them to give some commands. So everything was pending.” Interview: “[Previously,] I (Ba Co.) did not have any rules such as SOP. Mill A had a SOP because of ISSO. Other departments such as our department (information and system department) did not have any documents or regulations for us to follow. …In BETA Co., each person was expected to obey different kind of rules.” Interview: “In the past, I (Ba Co.) did not have the habit of doing paperwork. When I would like to buy something, …If I was in a bad mood, I just wrote the item on the paper and delivered it to purchasing department. If I was in a good mood, I would give a brief description.” Interview: “In Alpha Group, our salary was just close to or below the line (the regulations). [Moreover,] woman’s salary was less than man’s salary about twenty to thirty percent. …As everyone knows, BETA Co. pays well (more than the request of labor law). Even though they (employees of BETA Co.) are on holiday, the company (BETA Co.) still pays.” Interview: “According to the law, a person ascends a height more than 2 meters and there is no balustrade to protect him; he should wear a safety belt to prevent him from falling off. In Ba Co., everyone just obeyed the law. … BETA Co. is far away from what is normal. If you want to enter the mill, even though you just look around and walk on the ground, you should wear a safety belt, a safety helmet, and goggles. Everyone in the mill looks like a soldier of field forces. Too rigid!” Interview: “After our (Ba Co.) customers placed their orders on our products, they could receive our goods in four days. ...BETA Co.’s customers had to place their orders a month in advance.”. 學. Aggressiveness. Examples. BETA Group. ‧ 國. Organizational Identity Trustworthy. Ch. engchi. i n U. v. 30.
(31) Moreover, infrequent interaction further confirmed those perceived identity conflicts in group members’ minds and triggered real hostility between them and the newcomer. A vice president of Ba Co. in 2001 noted: In 2001, we once asked Bf Co. (a group-affiliated firm) to buy some raw materials for us.. After that. incident, the relationship [between our company and group affiliates] became more tense and hostile. … Bf Co. helped us to buy some raw materials.. These materials were already arrived, but we. decided not to execute this contract because we did not want to pay the money. Co. came to our company and intended to have a chat with our president.. The president of Bf. Our president refused to. meet him. He (the president of Bf Co.) waited outside until our president asked me to treat him to lunch. Then, he (the president of Bf Co.) told me that he hired some security guards to guard those raw materials at the main entrance for the sake of preventing people from taking those away.. 政 治 大 On the other side, according to one manager, people in Ba Co. felt lost and 立. lonely because they did not know who they are: “We were merged into the [BETA]. ‧ 國. 學. group. … [However,] when we read the newspaper, we were informed [that] they did We should be one of them but we felt lonely.. Some people among. ‧. not welcome us.. sit. y. Nat. us preferred to believe [that] we were still a member of Alpha Group.” The. io. er. awareness of enmity from the other side prompted people in Ba Co. to maintain original working styles, to interact with partners who they were used to get along with,. al. n. v i n and to be hostile to anyone fromC BETA Group. As one h e n g c h i U executive mentioned:” I once. tried to recommend Bd Co. (a group-affiliated firm) as our supplier who [took the responsibility to] maintain our production machines.. [Then,] I faced opposition. [coming from] all directions. … When their (Bd Co.) employees made some mistakes, some of us would put “disqualify” tag on them.” My interview data clearly indicate conflicts between two parties’ identities. Those perceived identity conflicts deteriorate into real hostility between conflicting parties when one party found the other party’s actions did not conform to or even violated a main and long-lasting part of their identity, and when one party did not have the opportunity to or refused to interact with the other party to understand the 31.
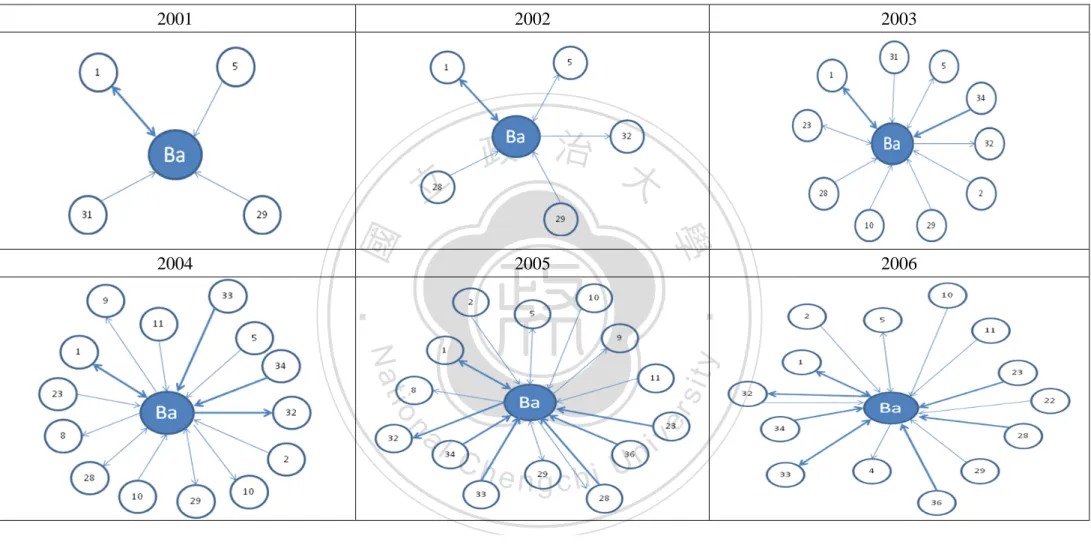
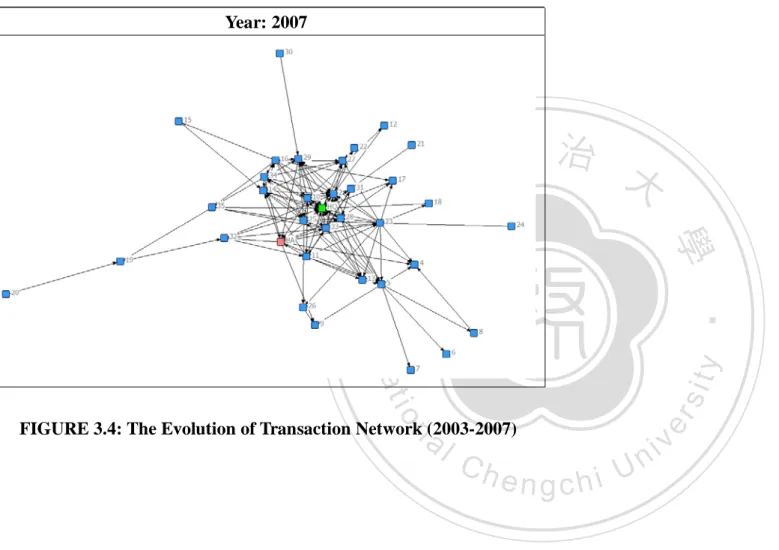
(32) thought behind negative stereotypes and negative attitudes towards them.. Interaction 1: Using friendships to bridge conflicting parties Although there was an atmosphere of great hostility and tension in the BETA Group, a desire of change gradually arose. production division.. This transition originated in Ba Co’s. The vice president of production division, who was dispatched. by BETA Co. in the early stage of acquisition, intended to break the deadlock and build friendships between his subordinates in Ba Co. and his friends who were the department heads in the group headquarters. recalled:. A general superintendent in Ba Co.. 政 治 大. 立. In the beginning, he (the vice president, production division) accompanied me (the general. ‧ 國. 學. superintendent, C. department) to visit the assistant general superintendent [C. department] and some managers in BETA Co.. He (the vice president) helped us to know each other. They (the assistant. ‧. general superintendent and managers in BETA Co.) promised that they would give us technical support when we sought advice on technical operations. … [Afterwards,] we once received a number of. y. Nat. complaints from customers about poor product quality, because we did not know how to smooth the oil. sit. on our products. I called him (the assistant general superintendent) and asked for his help.. n. al. er. io. he sent an expert to tell us the crux of the problem.. [Then,]. i n U. v. However, until 2003, such technical exchange happened on occasion, not an enduring relationship.. Ch. engchi. In addition, the boundary of interaction between two firms was limited. in production division. In 2003, the vice president was promoted to president and initiated a period of transition.. As figure 3.1 displayed, this promotion led to a dramatic improvement in. Ba Co.’s status in top managers’ friendship network. from the periphery to the center.. Apparently, Ba Co. moved. Although Ba Co. still performed the role of an. isolator in formal contacts such as transaction relationships, it did reach an enviable position in informal top executives’ contacts.. Figure 3.1 validated the president’s. argument: “I have some good friends (who are top management of group-affiliated 32.
(33) firms) in the group. I used these links to get them (people in the BETA Group) [to be] willing to have informal interaction with my fellows (employees of Ba Co.), such as providing some information about how to operate machines well.” The fact that, while there was hostility between two parties, the president began to exploit friendship to bridge them.. He tried to get his friends (top executives in BETA Group). on his side and create their willingness to give Ba Co. some support or interact with people in Ba Co.. Furthermore, building on friendships between top management, he. attempted to build friendships between employees of both sides.. As one executive. 政 治 大 Although he was a technician in BETA Co., we still learned a lot from 立. put it: “ Mr. Peng came to our mill and taught us how to modify the shape of sheet mental.. in the beginning.. We became brothers now.”. 學. ‧ 國. him. …He was sent by his superior (who was an old friend of the president of Ba Co.). ‧. On the other side, the president added incentives for people in Ba Co. to interact. y. sit. Conversely, BETA Co. (the group headquarters) was recognized as a center. io. er. output.. As explained above, Ba Co. was encumbered by low. Nat. with people in BETA Group.. of excellence in scaling up production; its volume of production has exceeded. solution to this problem.. Therefore, the president invited 3 technicians and 1. n. designed capacity by 40%.. al. v i n C h BETA Co. wasUable to provide a satisfactory Obviously, engchi. low-level manager in the group headquarters to Ba Co., acting as consultants, and let them get along with technicians all day long. more familiar with each other.. As time went on they were more and. One consultant in 2003 told us:. 33.
(34) President. Before. After. A. 立. 政 治 大. ‧. ‧ 國. 學. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. FIGURE 3.1: Top Managers’ Friendship Network (to be continued). 34.
(35) B. 立. 政 治 大. ‧. ‧ 國. 學 y. Nat. n. er. io. al. sit. FIGURE 3.1: Top Managers’ Friendship Network (to be continued). Ch. engchi. i n U. v. 35.
(36) C. 立. 政 治 大. ‧. ‧ 國. 學 y. Nat. n. er. io. al. sit. FIGURE 3.1: Top Managers’ Friendship Network. Ch. engchi. i n U. v. 36.
(37) In the early days, people from BETA Co. [,who came to Ba Co.,] were high up in the management hierarchy.. No one discussed technique with employees who were at the bottom of the hierarchy.. We. were the first batch of technicians. … [In the beginning,] we were viewed as intimates of the king [, because we were invited by the president]. …[Later,] there was a typhoon [which] devastated the mill; a nearby river flooded it.. Machines were submerged by flood water. We never knew our mill was so. fragile; the roof of the factory was lifted up by the typhoon. In that day, we didn’t go home and didn’t eat dinner. We stayed with them (employees of Ba Co.) to make urgent repairs all night….We took the lead to tighten canvases in order to block the wind….After the typhoon, we wrote many ideas to rebuild the mill.. For instance, we made a firm typhoon-proof door [which is] more solid than [that of]. BETA Co….[Afterwards,] they (employees of Ba Co.) gradually regarded us as brothers in adversity.. Additionally, these consultants progressively put BETA Group’s mind into practice.. 政 治 大 Before they (four consultants) joined us, we just sat there and watched the change at top management 立 level. We never deeply realized that one day we had to work with someone from BETA Co. and we One deputy general manager stated:. ‧ 國. 學. would change daily routines…[For example,] operation rate is an indicator to show whether machines malfunction. The denominator is the hours [that] machines should be in operation. The numerator is. ‧. the hours [that] represent line stop. In the past, we just calculated it (operation rate), but we did not track down a cause of malfunctions. …They (consultants) paid much attention on it. … In the daily. y. Nat. meeting, this issue (line stop) was discussed in more detail. We had to learn to list possible solutions. er. io. sit. and continually checked it.. In the next year, Ba Co. successfully broke through in the fight against production. al. n. v i n C his 2.4 million tons.U Ba Co. enhanced the volume The designed capacity engchi. bottleneck.. of production from 1.98 million tons in 2000 (the time of acquisition) to 2.53 million tons in 2004. Moreover, the volume of production has rocketed continually.. One. employee said:” I never dreamed that we would be able to go beyond the designed capacity.” Thus, in an era in which two parties refused to interact with each other because the negation of the salient part of the opposite side’s identity classified them into different groups, the president of Ba Co. tried to find ways to bridge them.. On the. one hand, he used his connections to create group members’ willingness to interact with people in Ba Co.. On the other hand, he began with the part, which was the 37.
(38) group headquarters’ specialty but Ba Co. could not overcome, to create his subordinates’ willingness to interact with group members.. Building on informal. links, technicians and managers in Ba Co. progressively learned some working practices or basic concepts from people who came from the group headquarters.. Identity 2: A shift in perceptions and usual practices As for members of Ba Co., thanks to the guidance provided by individuals from the group headquarters, they were able to progressively overcome all the obstacles in the area of production, which had been placed in their path.. As the production. 政 治 大. efficiency was beginning to improve and they were more acquainted with individuals. 立. from the other side, technicians and managers in Ba Co. gradually relaxed their. ‧ 國. 學. hostile attitudes to BETA Group and were willing to adopt relatively open minds to some practices and ideas which their friends, who belonged to the BETA Group,. ‧. poured into their knowledge pool.. As one executive noted,. y. Nat. sit. In the past, we did not need to record the current status of our machines and a history of maintenance.. al. er. io. The experience of machine maintenance was stored in maintenance workers’ minds. … [Afterwards,]. v. n. they (technicians from BETA Co.) implanted a sense of EAM (a machine management system. Ch. i n U. developed by BETA Co.) in our minds. We [learnt how to] code each machine separately and keep track of it.. engchi. Furthermore, as a vice president stated,” via internal rotation and an exchange of visits, such production-related practices, [which the group headquarters instilled into the central mill of Ba Co.], were diffused and adopted by other mills.” This shows that social interaction served as a catalyst for change.. People in Ba Co. gradually. accepted professional knowledge transferred from the group headquarters, adjusted their daily production-related routines, and redefined their own attitudes to the group. As for members of BETA Co., after interacting with the opposite side, they dispelled prejudice against Ba Co. because Ba Co.’s steady improvement in 38.
(39) production performance and its shift in working styles gradually changed their minds and diminished negative stereotypes.. As one supervisor noted:. The production in my mill is large in scale. We use seconds to calculate the volume of production. In BETA Co., it only took 120 seconds to produce a product. …[In 2000,] we need more than 200 seconds to produce a product.. After four consultants came [to our company], production rate [in my. mill] was 160 seconds. …[Subsequently,] we ever invited the heads of BETA Co.’s labor union to visit our mill.. They really appreciated our improvements.. Through social interaction, although conflicting parties did not change a large part of their identities or completely extricate themselves from an identity conflict trap On one side, 政 治 大 Ba Co. attempted to appreciate the opposite party’s merits and imitate the other side’s 立 yet, they did attempt to view one another as anything but the enemy.. good practices, especially in production area.. The opposite side, the group. ‧ 國. 學. headquarters, attempted to appreciate the transition in Ba Co., even though it did not. ‧. extend to the whole company.. y. Nat. io. sit. Interaction 2: Cutting off links with Alpha Group and expanding the boundary of. n. al. er. connections within BETA Group. i n U. v. As suggested above, social interactions motivated members in Ba Co. to review. Ch. engchi. usual practices whether they were outmoded or improper and to rethink what they believe defined the organization.. The movement towards a new definition of who. they are initiated a set of events that changed this picture dramatically. adjusted a portfolio of its partners.. First, Ba Co.. Ba Co. cut off links with Alpha Group to signify. that it decided to abandon its outdated thoughts, practices, and images.. At the same. time, it built links with members in BETA Group who could help it explore possible self. policy.. This partner selection decision represents a significant departure from previous As the president noted: “After the acquisition, our computer system still. connected to the Alpha Group…. I decided to cut this connection to prevent them 39.
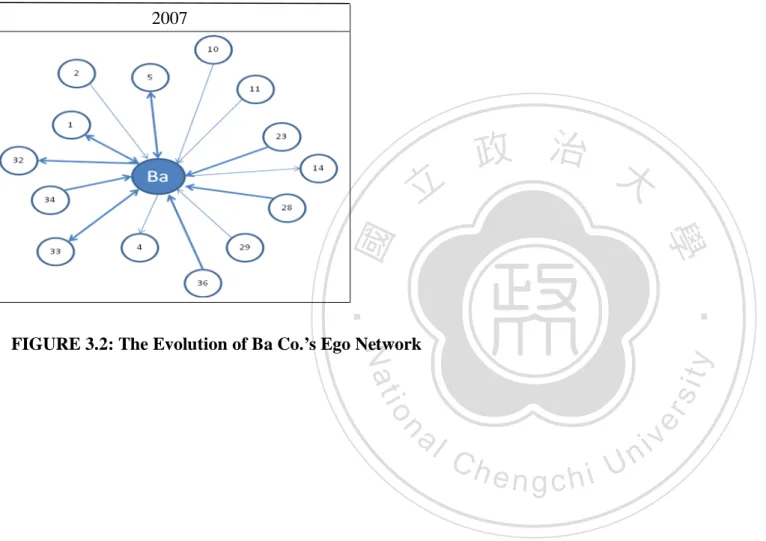
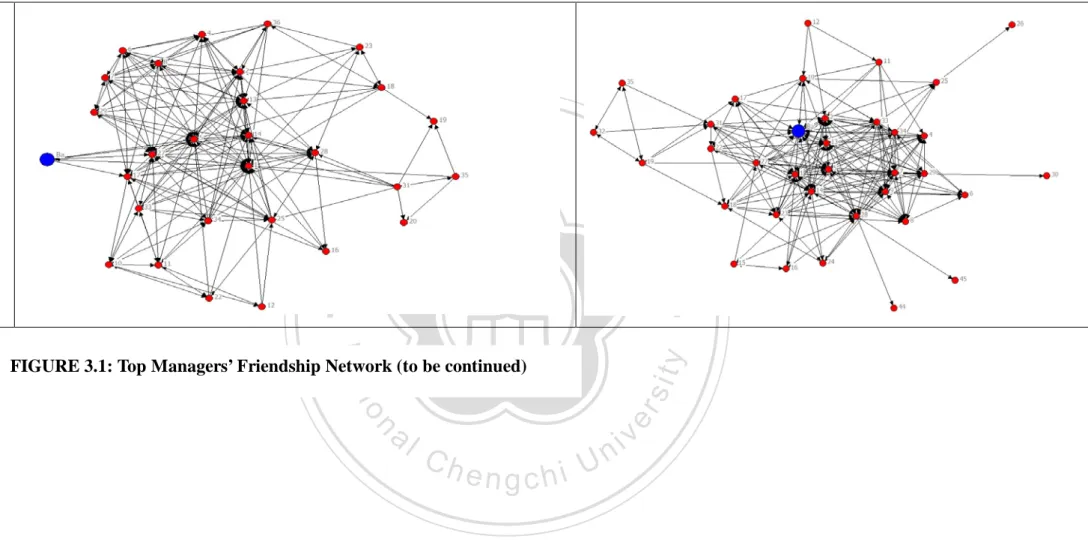
(40) from having our information in hand.. [Besides,] I would like to send a signal that. we completely broke away from Alpha group.” Subsequently, Ba Co. signed a contract with Bh Co. (a group-affiliated firm) which specialized in setting up information system such as Enterprise Resource Planning (ERP).. The president. stated: Originally, Bh Co. was a section of technology division of BETA Co. (the group headquarters).. [In. the past,] BETA Co. drew ERP into the group and implanted its management policy, thoughts, and practices in it. After several years, this section was spun off into a separate company, Bh Co. The experience of setting up ERP and the management thoughts and practices implanted in this system became the core competence of Bh Co… We decided to invite it (Bh Co.) to set up ERP.. This. 治 thoughts [which were developed by the decision represented [that] we also accepted those management 政 大 group headquarters]. 立 ‧ 國. 學. One executive illustrated the influence of ERP:. In the past, we did not have the habit of doing paperwork. When I would like to buy something, …If. ‧. I was in a bad mood, I just wrote the item on the paper and delivered it to purchasing department. If I. Nat. If I would like to buy spare parts, I had to fill out an. sit. form on-line if I wanted to take a day off.. y. was in a good mood, I would give a brief description. …[After the launch of ERP,] I had to fill in a. io. er. application form, including the provider, the item, the quantity, the reason, the application date, etc. … [Gradually,] we got used to it (ERP); everything has been well documented.. al. n. v i n C has a trigger for a series Apparently, partner selection acted of changes in Ba Co.’s engchi U usual practices which became progressively more consistent with those of BETA Group. Second, figure 3.2 displayed the evolution of Ba Co.’s transaction network. The dynamics of ego network change clearly indicated that Ba Co. actively and extensively built formal relationships with group members.. This connection. transition fully reflected Ba Co.’s attitudinal change and determination to adjust its partner portfolio for the sake of creating the feelings of membership and seeking appropriate and expected behavior which may give Ba Co. a new self-definition. Furthermore, the arrows in figure 3.2 showed that sister affiliates could sell products 40.
(41) and services to Ba Co.. As the president stated,” My principle was very clear.. would like to build enduring relationships with group affiliates. this message to my subordinates.. We. I also transmitted. Therefore, if the price range was reasonable, I. would choose group members as our providers.” Gradually, group members were aware that they could obtain strong support from Ba Co.. As one president of a. group-affiliated firm noted: ” When I were in financial straits, Ba Co. placed an order for our products to back me up.. This order touched us all deeply.. It gave me more. support than the group headquarters did.” The strategy of building extensive. 政 治 大 sister affiliates’ gratitude, and to push them to reconsider what this newcomer stands 立. connections with sister affiliates helped Ba Co. to show its attitudinal change, to win. for.. ‧ 國. 學. Third, by signing a technical exchange contract, Ba Co. further established. ‧. formal and frequent contact with the group headquarters, not merely informal Moreover, Ba Co. expanded the scope. sit. y. Nat. friendships and infrequent relations as before.. io. division.. As one general superintendent put it:. al. er. of contact, covering different functional areas in BETA Co., not merely the production. n. v i n C h division of BETAUCo.) to transfer technical knowledge We contracted with T division (the technology engchi to us…. [The function of] T division seems like a hub.. When we came to them for advice or expertise,. they would send individuals from varied functions or mills to us. …[For instance,] they sent people from T to help us develop oil drums. in good condition.. Technicians from W6 taught us how to maintain our machines. Brothers from Y5 gave advice on the improvement on product quality.. Such formal and frequent contact channeled not only technical knowledge but also non-technical ideas (such as shared values) into Ba Co.. Ba Co. was able to. reconstruct who they are with these new elements.. 41.
(42) 2001. 2002. 學. 2004. 政 治 大. ‧ 國. 立. 2003. 2005. 2006. ‧. n. er. io. sit. y. Nat. al. Ch. engchi. i n U. v. FIGURE 3.2: The Evolution of Ba Co.’s Ego Network (to be continued). 42.
(43) 2007. 立. 政 治 大. ‧. ‧ 國. 學. n. al. er. io. sit. y. Nat. FIGURE 3.2: The Evolution of Ba Co.’s Ego Network. Ch. engchi. i n U. v. 43.
(44) As we mentioned before, in identity 2, informal contact gave Ba Co. an opportunity to make a comparison of production-related practices between both sides, to learn from the group headquarters, and to further change its attitude towards BETA Group.. Clearly, informal contact breeds attitudinal change.. Such attitudinal. change further initiated a series of shifts in the combination of connections via partner selection.. First, departing from a prior way of choosing partners, Ba Co. cut off. links with original partners such as Alpha Group to abandon outdated images but, meanwhile, built the links with BETA Group affiliates to explore new and possible. 政 治 大 thoughts and practices which gradually conformed to those of BETA Group. 立. self-definitions.. The choice pushed Ba Co. to step forward on the way of changing. other affiliates gratitude and affection.. On the one hand, it won. 學. On the other hand, it pushed other affiliates. to rethink what this newcomer represents.. Third, Ba Co. built more formal and On the one hand, staffs had. sit. y. Nat. diversified connections with the group headquarters.. ‧. ‧ 國. Ba Co. established extensive relations with sister affiliates.. Second,. io. er. more opportunities to interact with or learn from individuals coming from varied functional areas or mills in the group headquarters. On the other hand, the group. al. n. v i n headquarters progressively and C imperceptibly instilledU h e n g c h i shared values or common characteristics in Ba Co.. Identity 3: Co-evolving similar characters and exploring distinctive characters When the group headquarters attempted to pour new elements (shared values and common characteristics) into Ba Co.’s identities, Ba Co. experienced a suffering period.. For example, in the past, there were few rules for Ba Co.’s staffs to follow.. Under the circumstances, the purchasing department grasped great power because all purchases should route through it and few rules could regulate it.. One consultant. from the group headquarters recalled: 44.
(45) In an evening, we needed to rent a crane to fix a machine.. It was an emergency.. general superintendent [of this mill] to telephone the crane company.. I requested the. He said: “Wait a moment.. I. needed to call the purchasing manager first to gain his permission.” … I was very surprised [that] a general superintendent (a higher position in the hierarchy) should report to a purchasing manager (a lower position in this hierarchy).. It never happened in BETA Co.. On the contrary, in BETA Group, individuals were expected to adhere strictly to the rules.. A statement from one manager illustrated the differences between two groups:. [In the past,] the purchasing department [in Ba Co.] always bought something different from what I suggested; they (staffs in purchasing department) bought it because it was cheaper. [However,] I got annoyed when I used it….I ever told them my feelings when I got something which was against my expectations. They replied:” You never used it before.. How do you know [that] it must be a. 治 regulations,] although I needed to fill troublesome item?” … In BETA Group, [under 政the purchasing 大 out a form on-line, purchasing department mostly adopted my suggestions and bought what I desired. 立 ‧ 國. 學. Through social interaction, technicians and managers in Ba Co. had the opportunity to know BETA Group’s practices and thoughts, to make a comparison, and to realize that. ‧. they needed to make some changes.. One executive who tried to reform the. sit. y. Nat. purchasing system told us:. al. er. io. Previously, when we bought an unsuitable machine, no one had to take the responsibility.. As for us. v. n. (people in production division), purchasing department did not follow our suggestions so it was not our. Ch. i n U. fault. As for them (staffs in purchasing department), they never worked in the mill so they did not. engchi. know it was an unsuitable machine….In BETA Co., there was a very clear policy.. [First,] each mill. had the authority to outsource some work to some cooperative providers directly.. Second, if they. (people in the mill) would like to buy something which they could design and domestic manufacturers could follow the composition to produce it. W6 (the central maintenance shop) would deliver the draft to appropriate manufacturers. Third, if they would like to buy something such as a gear wheel which should be bought from foreign companies, the purchasing division would do it….[Obviously,] we also needed a clear rule [to terminate this chaos].. I attempted to propose changes to the. purchasing system in management meetings… The initial reaction of the purchasing manager was “This company does not need the purchasing department any more.. The purchasing department can. be cancelled now!”. To start with, Ba Co. contracted with some BETA Co.’s cooperative providers. According to the contract, Ba Co. could follow the example of BETA Co.; namely, 45.
數據
Outline
相關文件
First, this research integrates academic literature from management information systems, strategic management, knowledge management, and organizational theories, based on
• Introduction of language arts elements into the junior forms in preparation for LA electives.. Curriculum design for
據美國的研究指出網上體育課一般都以體適能為主 (Fitness-focused), 但主要的學習成果以認知 多於技能 (difficult to provide real-time psychomotor feedback, which is invaluable
According to the passage, which of the following can help facilitate good sleep for children.. (A) Carefully choose the online content
在選擇合 適的策略 解決 數學問題 時,能與 別人溝通 、磋商及 作出 協調(例 如在解決 幾何問題 時在演繹 法或 分析法之 間進行選 擇,以及 與小組成 員商 討統計研
分析 分析 分析(Analysis) 分析 分析 組織 組織 組織 組織/重整 重整 重整 重整 綜合.
在選擇合 適的策略 解決 數學問題 時,能與 別人溝通 、磋商及 作出 協調(例 如在解決 幾何問題 時在演繹 法或 分析法之 間進行選 擇,以及 與小組成 員商 討統計研
y 2002年,UNICEF,UNESCO, WHO 三個聯合國組織共 同建議各國中等學校應認知21世紀是一個資訊量